This article is more than 1 year old
Suckfly: The hacking group targeting India but taking weekends off
State-sponsored hackers without overtime?
A professional hacking group called Suckfly is targeting India's infrastructure and economic base by zeroing in on individuals and installing tools to access their work networks.
That's according to a blog post by Symantec that has analyzed and dug into the group's activities and methods.
Symantec first spotted the group it has called Suckfly targeting South Korean organizations in March this year in an effort to steal digital certificates. It followed their trail through their custom malware and found they had been methodically targeting key organizations in India, both governmental and commercial.
The malware – called Backdoor.Nidiran – has been found in disproportionate numbers in India. Symantec did not name the targets but did note that one of India's largest financial institutions is among them, another a top five IT firm, another a large e-commerce company, the Indian business unit of a US healthcare company, and two government organizations.
The target the hackers spent most time on was a government department that installs network software for other ministries and departments – the advantage to hacking into its systems being obvious.
Symantec also managed to uncover the group's attack method: they found an employee at each organization that had a significant online footprint and installed their malware on their system – Symantec reckons a phishing attack was the most likely approach.
The malware then uses known security holes – in this case unpatched Windows flaws – to escalate privileges before posing as that individual to enter their work network. Once in the network, the attackers looked for other targets and ultimately sent out as much data on the internal network as possible to a number of hardcoded servers controlled by the group.
The group is sufficiently organized and patient for Symantec to conclude that it is a professional hacking group with a specific mandate. But perhaps the most telling proof that it's a professional group and not amateur hackers is the fact that it was possible to analyze the instructions sent by day and time and there was no activity at all on weekends. In other words, it's a Monday to Friday, nine-to-five job for somebody.
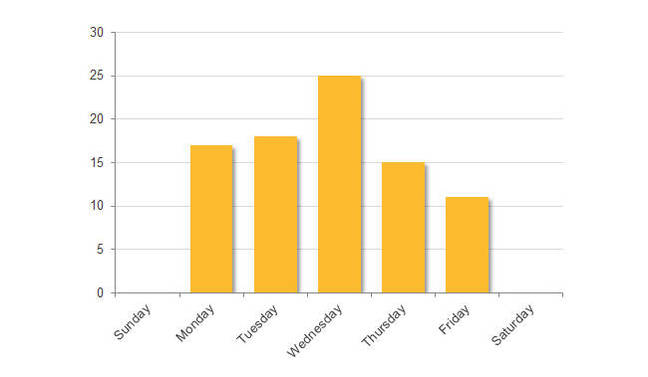
Clocking in and out: these hackers have weekends off.
Who is Suckfly and where do they come from? Symantec doesn't even attempt to guess but it notes its targets have been South Korea – for certificates – Saudi Arabia, and India, with India by far the greatest target.
What is noteworthy is that the domains used to receive information have English spelling, some clearly posing as legitimate domains such as fedora-dns-update.com and microsoft-security-center.com.
There are some other pointers that may mean something or may mean nothing. Several of the domains were registered through a Yandex email address, for example. Yandex is based in Russia.
It could be a government-sponsored hacking group – the best known examples being in China and Russia – or a freelance group paid for their efforts. The targeting of India's economic and governmental centers could benefit both foreign governments and those looking to make money from commercially sensitive material, so motive is also hard to divine.
What is worth noting, however, is the concentrated effort and sophistication involved. Symantec only uncovered the attacks two years after most of them had taken place and only then after it knew what to look for. ®
