This article is more than 1 year old
Palo Alto IDs another C&C-over-DNS attack
'Pisloader' hides instructions in plain sight
Palo Alto Networks researchers say the Webky group is using DNS (domain name system) requests as their command and control channel.
The reason that's important is that DNS is one of those ports that's less heavily policed than (for example) Port 80.
The Palo Alto post (by Josh Grunzweig, Mike Scott and Bryan Lee) says the activity was spotted during an attack on an unnamed US organisation.
The attack was based on the HTTPBrowser malware family, which was seen in attacks such as this from 2015 in China.
The researchers dubbed this attack 'pisloader'. It pointed victims at http://globalprint-us[.]com/proxy_plugin.exe to download malware, which loads the well-known Poison Ivy RAT.
The other domains used in the attack, all newly-registered, were logitech-us[.]com (not the real Logitech), and intranetwebcam[.]com.
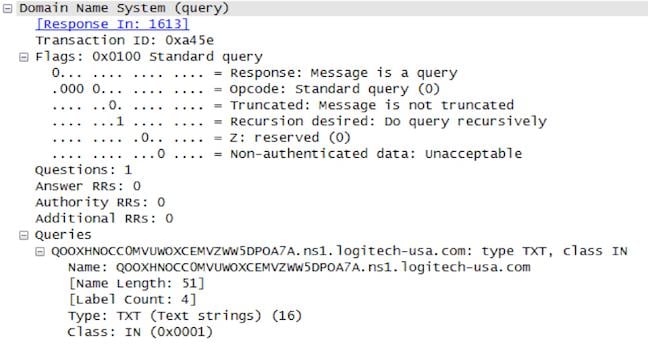
It's mostly the DNS C&C that makes this different, Palo Alto Networks writes. Here's an example of the request:
Like FrameworkPOS, putting C&C instructions in the protocol is designed to skip past security products.
Hence a response from the C&C will be in the form of a DNS response, with instructions to the malware in the text of the response:
- sifo – collect victim system information;
- drive – List drives on victim machine;
- list – List file information for provided directory;
- upload – Upload a file to the victim machine; and
- open – Spawn a command shell.
As the post notes, the code to generate the commands is at GitHub. ®
