This article is more than 1 year old
Boffins shake up smartphone with motion-sensor as microphone
I'm picking up good vibrations, I'm listening to excitations
University of Illinois boffins have proved that someone who steals your phone can perform hardware hacks on it.
As a maker-hack, The Register can't help but admire the work done to create the “VibraPhone” (even the pun is better than average). As a security vulnerability, we'll file this under “if you lose your phone, you're p0wned anyway”.
Perhaps the most serious detail in the research is this: because nobody regards the vibration sensor as sensitive, smartphones typically leave it with wide-open permissions.
What Nirupam Roy and Romit Roy Choudhury did was to hack an Android phone so its vibration sensor acted as a microphone. Well: a vibration sensor is half-way to being a microphone anyhow, in terms of its basic function.
As they note in this paper, “any vibrating object should respond to air vibrations”. What makes a microphone different is that the diaphragm is very light, and therefore responds well to quiet sounds and high frequencies. The vibration sensor, on the other hand, doesn't respond much to either.
As the pair says in their paper, “VibraPhone is attempting a different problem altogether – instead of learning a motion signature, it attempts to reconstruct the inherent speech content from the low bandwidth, highly distorted output of the vibra-motor.”
And, as they demonstrate here, they succeed.
To get there required experimentation with a vibra-sensor outside the phone (below) to get a handle on what behaviour they might expect.
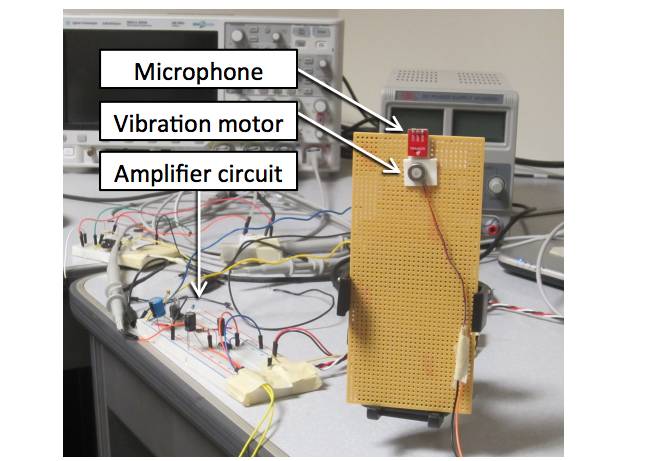
A vibration sensor compared to a microphone
That was followed – tinfoil-hatters take note – by a fairly extensive modification of a Samsung handset. The Register would observe that any spy agency who's got your phone long enough to do this doesn't really need VibraPhone's help.
The hardware-hack is necessary, since while the vibration sensor isn't guarded by permissions, it lacks the necessary connections to act as a microphone:
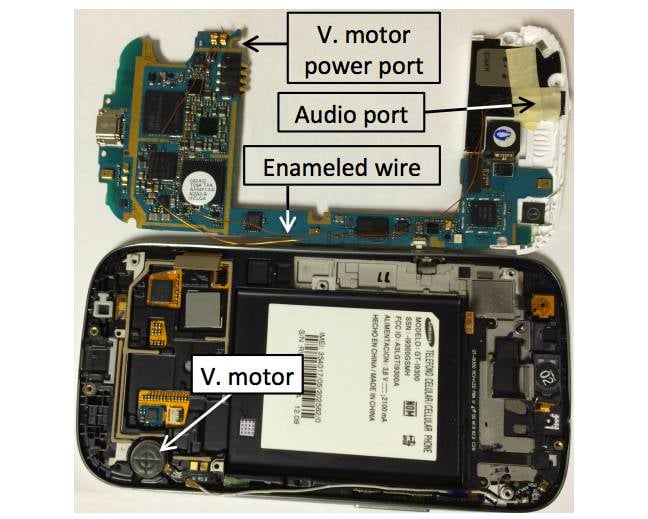
If the spooks can do this to you, you're already p0wned: the connection from the vibration sensor to the line in port
“Finally, we emphasise that smartphone vibra-motors cannot be used as microphones today, primarily because the actuator is simply not connected to an ADC”.
Then there's the signal processing, including equalisation, background noise treatment, and separating the speech energy from the background noise they couldn't get rid of.
While the “spooks can spy without the microphone” angle is irresistible, what's more intriguing is the authors' notion that apps could be built to give voice control to wearables (like Fitbit) that don't have microphones.
The research will be presented at the ACM's MobiSys '16 conference in Singapore later this month. ®
