This article is more than 1 year old
Parliament takes axe to 2nd EU referendum petition
Names removed, but 'no fraud'
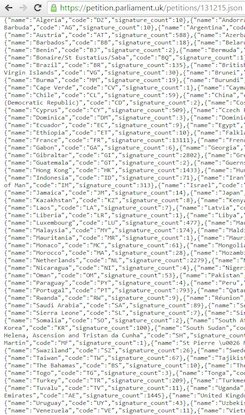
Analysis A petition to nullify the UK’s EU referendum and hold another appear to be riddled with fraudulent data. Raw data examined reveals that many of the participants come from outside the UK, or use IP addresses outside the UK. Only UK or British citizens and residents can create or sign a petition, according to the rules. You can see the geographical breakdown here.
Some 39,411 signatories came from Vatican City, even though the city state has a permanent population of only 450. Over 23,000 voted from North Korea.
The House of Commons petitions committee is investigating the petition for fraud, and has already removed 77,000 “signatures” - but says the site was “not hacked”. The petition, ironically created weeks ago by a Leave campaigner, calls for the vote to be rerun if turnout was under 75 per cent, or the winning plurality was under 60 per cent. It has reached 3.6 million signatures.
However the geolocation data for the votes can easily be examined.
Although the UK’s voted to leave the EU with a clear democratic majority of on a turnout of 72.9 per cent, the petition to change the rules after the fact was promoted by the BBC’s Brian Cox and former Guardian editor Alan Rusbridger.
A rather mischievous question ... what happens if over 17 million people sign the petition for a second referendum? https://t.co/O9GhhL3M6R
— Brian Cox (@ProfBrianCox) June 25, 2016
EU Referendum rules petition heading towards 3m signatories Live feed here https://t.co/HuwS7ryLL8
— alan rusbridger (@arusbridger) June 26, 2016
My team in Panama added about a million of these. Great work #proud https://t.co/RbqDU4pCfp
— (((Steve Bong MBE))) (@BongVentures) June 25, 2016
“The sight of educated men and women trying to overturn a national referendum with an online petition is pathetic beyond belief,” wrote Chris Snowdon of the Institute for Economic Affairs. “Many of the arguments made by the Remain camp were fundamentally anti-democratic; they prefer to have an elite in charge with whom they agree [rather] than have a demos in charge with whom they do not. Since losing the referendum, their contempt for democracy and the demos has become terrifyingly explicit. Every attempt is being made to find a way of overruling the will of the people.”
Helen Jones MP, Chair of the Petitions Committee, said MPs would discuss whether the petition could trigger a Parliamentary debate. Not all do. ®
Bootnote
No doubt some signatures are valid. Your reporter's school class lists here in leafy North London - a bastion of middle class Remain supporters - were hijacked by parents urging others to sign the Second Referendum petition. Normally parents admonish their children for throwing their toys out of the pram.