This article is more than 1 year old
Here's how to SMS spam Liberal voters and get away with it
Bulk SMS sender, Tails, Tor, and some free WiFi
It's easy to spam voters with text messages and get away with it.
If you wanted to swing voters ahead of a federal election, as the Australian Labor Party is alleged to have done in a message claiming a rival Liberal Coalition Government would privatise the nation's healthcare provider Medicare, you wouldn't send a text message from campaign-linked phones.
That would make the job of the Australian Federal Police too easy. The feds are now investigating the incident which occurred during Australia's federal election period, the results of which are still neck-and-neck.
Labor campaign headquarters says the text messages were in line with its party propaganda messaging.
The texts had the MMS subject of 'Medicare' with some recipients believing the message was sent from the government health agency.
But you're smarter than to get caught, so instead you first turn to Google. Try it yourself; type 'bulk SMS no registration' and enjoy filtering through the many paid and free offerings available.
Select one that is offshore, preferably.
But don't send your text just yet.
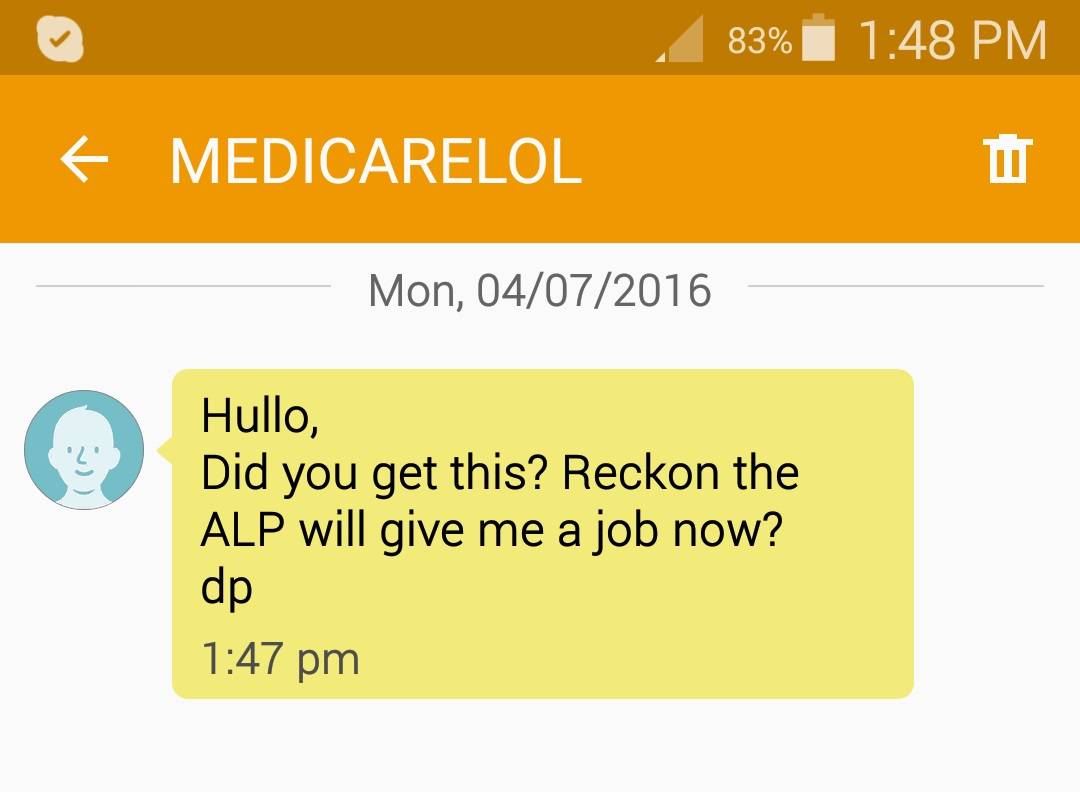
Reg hack Chirgo gets a text.
Grab that cheap burner laptop bought off Gumtree you've never used with Tails installed and jump on some cafe wifi three towns over. Fire up Tor.
Browse to your bulk SMS site, register with a throwaway email account and garbage credentials, buy credit using your anonymous currency of choice, be it bitcoins or virtual credit cards, and load up your database brimming with voter victim phone numbers.
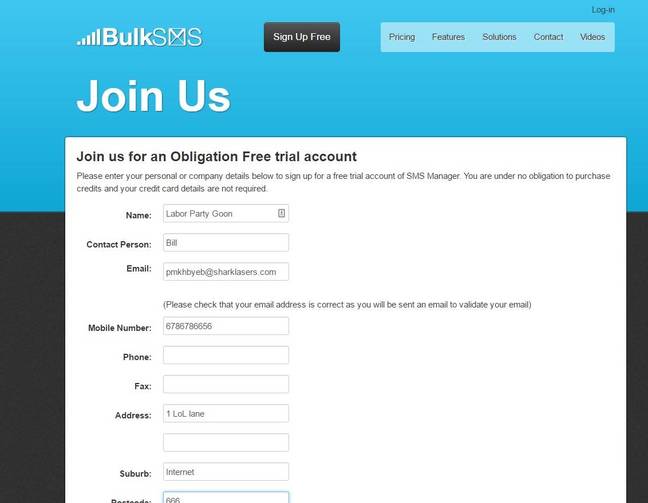
Enter your details.
Fret over the number of CCTV cameras you walked past.
All of this is of course nothing new, and there are doubtless better operational security tactics to pursue.
Mobile numbers in Australia can also be spoofed to appear sent by any number, which this author may have tested for research purposes on unwitting mates. ®
