This article is more than 1 year old
Outed China ad firm infects 10m Androids, makes $300k a month
Check Point slayers reveal building address, pop panels, publish office floor plan.
Net scum behind the Hummingbird Android malware are raking in a mind-boggling US$300,000 (£233,125, A$404,261) a month through illegitimate advertising and app downloads from a whopping 10 million infected devices.
The offending group, known as Yingmob, is an offshoot of a legitimate Chinese advertising analytics firm with some 25 staff dedicated to building HummingBad's malware componentry, and appears to be one of the most successful and capable groups in the mobile malware business .
Check Point researchers tracked the company to its offices in Chongqing, China. It even obtained the seating plan of the office and organisational structure.
Yingmob has produced some of the most capable and lucrative mobile malware for Android and iOS devices.
Its combined legitimate and outright malicious applications, the latter class representing a quarter of its output, are installed on a massive 85 million devices.
This huge number has been achieved since only August, according to Check Point researchers who obtained access to YiMob's control panels.
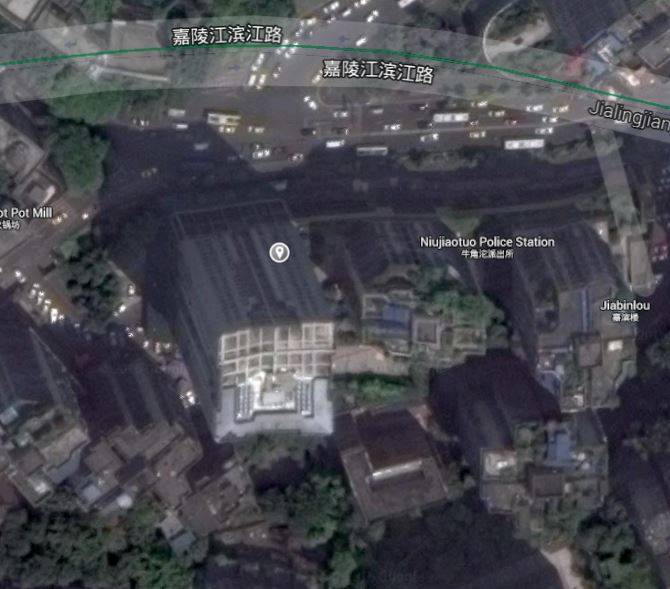
The Xingdu Plaza offices. Google Maps / The Register
.Yingmob staff are split into three teams including developers dedicated to building malicious componentry, the ad server analytics platform, and the ad server application package (apk).
"After analysing most of the apps on the dashboard, the research team estimates that nearly 10 million users are using these malicious apps," Check Point threat researchers write in a report [PDF].
"Yingmob may be the first group to have its high degree of organization and financial self-sufficiency exposed to the public.
"Check Point believes this dangerous trend will escalate as other groups learn from Yingmob and find new ways to achieve the independence they need to launch larger and more sophisticated attack campaigns in the future."
Hummingbad once downloaded to Android devices through malicious applications will attempt to root phones -- a risky process which can at worst brick devices and at best void warranties -- and failing that request sufficient administrative access to fully compromise devices.
Infected devices will display a share of the company's 20 million ads displayed daily which combined attract 2.5 million clicks.
The handsets will also install a portion of some 50,000 fraudulent apps a day using simulated clicks in the Google Play store. All told the fraudulent clicks and app downloads contribute US$10,000 (£7771 A$13,475).
Check Point's access reveals China and India have each 1.6 million and 1.4 million devices running Hummingbad. The United States has 286,800, while Britain and Australia were not listed in the top 20 infected countries, meaning the nations have less than 100,000 compromised devices.
Half of all Hummingbad-infected users run the horribly outdated KitKat version 4.4 operating system, which is the second most popular version capturing 31.6 per cent of Android users.
About 40 per cent run the significantly more secure Lollipop version 5.x operating system, which is the most popular running on 35.4 per cent of Android devices.
Access to YiMob's control panels reveals the company registers some 200 derivative apps which a quarter are malicious
The group is also credited with producing the first iOS malware capable of plundering non-jailbroken Apple devices known as Yispecter.
That cocktail of iOS 8 plundering weaponry targeted since-fixed enterprise certificate holes to, like Hummingbad, generate revenue by displaying advertisements and downloading applications. ®
