This article is more than 1 year old
Florida U boffins think they've defeated all ransomware
Crypto Drop looks for tell-tale signs that files are being encrypted
Researchers from the University of Florida and Villanova University reckon ransomware can be stopped by watching what it's doing to the target's files.
Taking a “save what you can” approach, the authors of this PDF reckon in their tests they were able to lower the boom on ransomware when it had encrypted just 0.2 per cent of files on their test setup.
The paper identifies three primary indicators that a program is encrypting files against the user's wishes:
- Bulk modification of file types;
- Dissimilarity – the encrypted file looks nothing like the plaintext. This, after all, is a characteristic of all encryption;
- Entropy – encryption should produce consistently high entropy in its output.
- Secondary indicators – there are secondary indicators that can support the three above, such as deleting files in bulk; file type funnelling, in which everything the malware produces results in the same type of file.
To support the second primary indicator, the similarity measurement, the researchers use a tool called sdhash which produces a similarity score between two files – in this case, the unencrypted and the encrypted file.
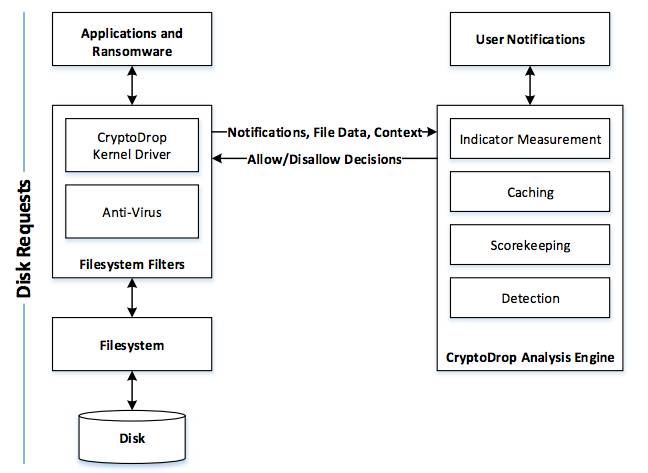
Crypto Drop architecture
The researchers reckon their median performance for all samples was 10 lost files out of a total of 5,099 – 0.2 per cent.
The paper notes that in its current state, Crypto Drop has to rely on the user to distinguish between legitimate activity (encrypting files with PGP or a compression tool) and an attack.
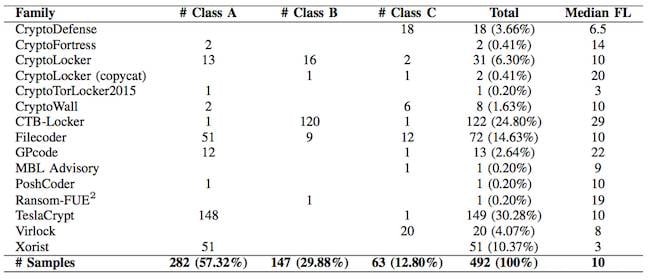
Ransomware families tested against Crypto Drop
Even if that can't be eliminated, Vulture South is sure anyone who's received a ransom note and paid a Bitcoin to recover their files would rather click a dialogue saying “it's okay, I'm zipping the files” instead of coughing up.
The research was presented to the recent IEEE ICDCS conference in Japan. ®
