This article is more than 1 year old
CloudFlare probes mystery interception of site traffic across India
Traffic to Pirate Bay and others redirected to AirTel banned URL notice
An unknown agency in India, possibly telco Airtel, is quietly capitalising on encryption gaps in sites tended by DDOS-buster CloudFlare to intercept and redirect users.
Little is yet known about the attacks, so far detected targeting piracy torrent site The Pirate Bay and a handful of other outfits.
CloudFlare engineers have, at the time of writing, emerged from an emergency meeting to investigate the now verified claims that traffic to their customer sites is being intercepted.
Visitors to intercepted websites are redirected to an AirTel page which reads that the "requested URL has been blocked as per the directions received from Department of Telecommunications, Government of India".
The redirect page does not necessarily confirm that the interception is the handiwork of AirTel.
India has blocked sites for nearly two decades without formal policy, but it is the first time it has so directly capitalised on absent security measures to deny access to a URL.
Some of CloudFlare's sites include those run by political dissidents, hacking forums, and piracy sites. Such sites are often in the crosshairs of governments.
India-based developer Abhay Rana (@captn3m0) and security researcher Shantanu Goel (@shantanugoel) discovered Pirate Bay traffic interception which they suspected may be thanks to cooperation between CloudFlare and the Indian Government, or due to security flaws on behalf of the anti-distributed denial of service attack provider.
CloudFlare founder Matthew Prince told The Register that the company concluded a meeting less than an hour ago and says there are no security flaws on its side, but that the company was blind-sided by the interception.
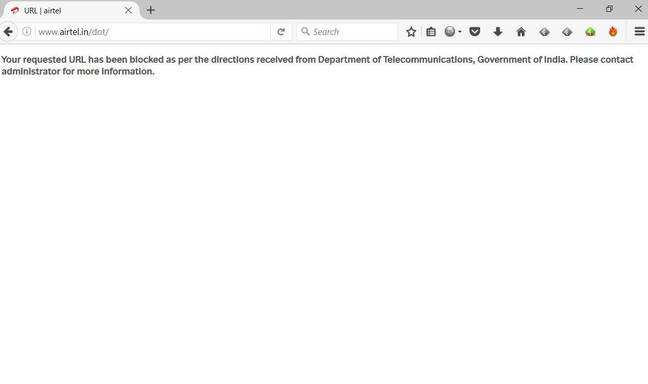
The redirection landing page.
Prince says the attacks occurred at CloudFlare's Chennai and New Delhi data centres but not at its Mumbai point of presence.
"It appears to only affect traffic that is being passed over an unencrypted link," Prince says.
"Whatever the system is that is looking for the requests might not be installed in Mumbai, we don't know, but it appears to be triggered off the host header in requests.
"It suggests there is some system that is running either at the edge of India's network or within AirTel that is at least conducting infection of host headers in requests."
Prince says the company is examining "all traffic" to locate other affected customer sites, but did not name impacted clients.
The company offers free and paid distributed denial of service attack mitigation and uptime and anonymity services to a host of web properties.
The Indian Government may have reason to target CloudFlare customers.
The tech company has since 2014 offered its paid enterprise distributed denial-of-service mitigation services to established political blogs, news sites, and other public interest organisations for free under Project Galileo.
AirTel representatives contacted by CloudFlare were not aware of the interception but are investigating the matter.
The Register has contacted the company for comment.
Prince says interception is seemingly possible only for sites that do not use encryption on origin servers.
CloudFlare in May asked customers to install its free certificate to help admins accomplish the task.
Writer Karthik Balakrishnan has further analysis of the attacks which CloudFlare has largely vetted as accurate, sans its claimed intentional involvement or security flaws.
We'll update this story as and when more detail emerges. ®
