This article is more than 1 year old
OneLogin breached, hacker finds cleartext credential notepads
'Store your firewall password here' notes pillaged
Password attic OneLogin has been breached, and it's bad, because the service that suffered the breach is one often used by people to store credentials like admin password and software keys.
The online credential manager says its Secure Notes facility was breached, allowing the intruder to read in cleartext notes edited between 2 June and 25 August this year.
Some 12 million customers use OneLogin.
It could be a dangerous breach for those affected. OneLogin suggests Secure Notes can be used to hold "information such as license keys and firewall passwords" making the stolen data a gift for network exploitation and lateral movement, should IT folks heed the advice and store sensitive credentials in the service.
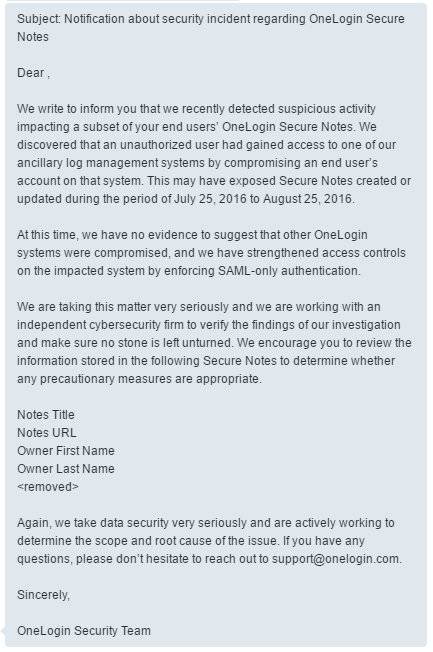
OneLogin has offered a breakdown of the incident blaming an unspecified bug for allowing user note entries to be visible in its logs prior to being slapped with "multiple levels of AES-256 encryption".
It says the offending hacker stole a staffer's password by means undefined and used it to access company internals.
The company has been contacted for comment.
"Based on the activity in the log management system, we can see that the intruder was able to view, at a minimum, notes that were updated during the period of July 25, 2016 to August 25, 2016," chief information security officer Alvaro Hoyos says in a statement.
"Due to the presence of the intruder as early as July 2, 2016, we are advising customers that notes updated during period of June 2, 2016 to July 24, 2016, are also at risk."
The service has reached out to affected users it says accounts for a "small subset" of its customers.
OneLogin has recruited an unnamed external security company to ensure it has adequately mopped up after the breach.
The clean up includes restricting access to the affected log management system to SAML-based authentication and from a whitelist of IP addresses, and resetting all internal system passwords that do not already adhere to that level of security.
"Again, our most sincere apologies. We are making every effort to prevent any similar occurrence in the future," Hoyos says.
Google Project Zero researcher Tavis Ormandy has turned his prolific breach blunderbuss on password managers of late, finding the cloud-based variants to be woefully insecure and a technology to be avoided.
He recently found since-patched zero-day vulnerability in password vault LastPass that exposed scores of users.®