This article is more than 1 year old
Hackers claim they breached Aussie point-of-sale tech firm, try to sell 'customer DB'
Claim to have backdoored supplier to Woolworths' pub chain
Exclusive Hackers are claiming to have hacked Australian point-of-sale technology (PoS) company H&L Australia, and have been claiming to potential buyers that they had lifted its customer database. They were already offering it for sale for AU$22,000 ($16,580, £12,723) more than two months ago.
If indeed they have hacked into H&L, credit card data and personal information would potentially be at risk: the firm's clients include several major retailers.
The Register received information about an alleged breach at H&L Australia two weeks ago, plus the credentials required to access what was alleged to be an active backdoor on the company's network and an open public link to a large SQL database dump.
We immediately reported this to CERT Australia, which offers assistance to compromised businesses.
Our information came from Alex Holden, founder of US-based intelligence company Hold Security.
Holden has form disclosing large breaches and has significant access to underground crime forums. He provided The Register with a chat room exchange between two unnamed entities he says were buying and selling what was purported to be the "H&L Australia database".
The message thread spans almost four hours on 18 July. In it the hackers chat in broken but succinct English.
The exchange between the two was as follows:
| 11:23:53 seller: "http://URL.hlaustralia.com.au. have shell"
11:25:00 buyer ok , also will need admin cp (control panel) and db (database) 11:25:11 buyer i will make deal about it when my guys comes online ... 14:52:29 buyer password of shell hlaustralia 14:52:33 seller admin 14:53:46 seller all site of hlaustralia.com.au on one server 14:54:21 buyer good |
|---|
The shell and database – allegedly of H&L – was to be sold to the buyer for 27 Bitcoins on 27 July.
The apparent backdoor and claimed stolen database have since been removed. At no point did The Register access the alleged "backdoor" or the database.
We have made repeated requests for comment to H&L Australia, the first on September 13. The company has not responded directly to our questions, but in correspondence does not dispute the breach and indicates it is taking action to inform stakeholders about the situation.
If a theft took place, precisely what was stolen is uncertain, but Holden claims he's aware of a 14.1Gb database dump, purportedly from the company.
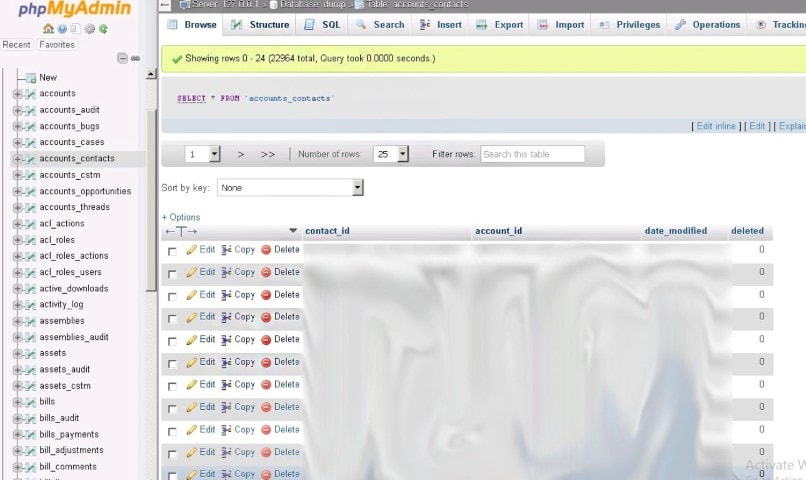
The supposedly breached local server database – according to a screenshot of the alleged dump – includes fields login; mortlock; password; homer16; db name, and hnlial_db.
H&L's customers include Australian Leisure and Hospitality Group (ALH), a venture that operates some 330 pubs and clubs around Australia.
Supermarket giant Woolworths is a joint-venture partner in ALH. Neither Woolworths nor ALH responded to repeated requests for comment after confirming initial receipt of news of the alleged breach on 13 September.
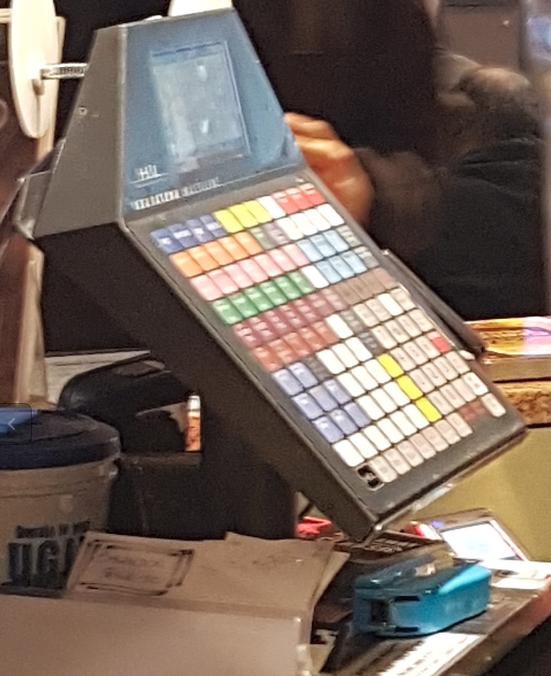
A H&L Australia terminal in an AHL pub. Image: The Register
Time for a stiff drink
Australian pubs are well patronised, so if the allegations are true, there's potential for many individuals' details to be in the data dump.
Neal Wise, director of Melbourne penetration testing firm Assurance.com.au says the potential impact would depend on the information contained in alleged stolen databases, adding that PoS platforms are linked often to other systems such as loyalty programmes, which would potentially expand the scope of the client impact.
"I’m not sure what data has been accessed so this could be as simple as enabling 'classic' credit card fraud or it could tie back into loyalty or other related systems," Wise says.
Other security experts speaking on the condition of anonymity agree it is reasonable to conclude that the hackers would seek to monetise the valuable intelligence they would have paid a high price to acquire and those whose details have allegedly been collected at the point of sale.
They say that if the hackers are telling the truth, they might be able to use the database to compromise customers' information – including credit card or personal staff and payroll information – although nor the The Register nor experts contacted for the story could legally download and inspect the database, beyond viewing a screenshot purported to be of the database that the hackers uploaded to the internet.
The oldest trick in the book
If the alleged breach took place, it is likely the hackers located a file upload or SQL injection vulnerability to create the backdoor in firm's systems, a form of attack Holden describes as the “oldest trick in the book”.
The Federal Government's CERT Australia, while not commenting directly on the alleged breach, says organisations need to harden their defences.
"All organisations, including small and medium businesses, need to consider cyber security as part of their day-to-day business," the agency told The Register in a statement. "Businesses that become aware of cyber security incidents should contact CERT Australia."
The agency in 2014 published a guide for information security controls recommended for small- and medium-sized businesses. The advice, if followed, will significantly reduce exposure to compromise. It should be paired with advice within the Federal Government's Stay Smart Online website.
The Open Web Application Security Project also offers security advice describing the worst perennial web application holes and mitigation strategies in its Top 10 list.
Wise says PoS systems must be segregated from other premise networks.
"Basically avoid combining venue networks - guest wireless, PoS terminals, etcetera," Wise says, citing an example of a dentist who ran the sensitive office network on the same LAN as his guest wireless.
"Also remember that if you have systems that interface with bookkeeping and supply chain those should be protected and should be deployed in network segments that strictly control their access."
Wise says PoS vendors should ensure data is protected at rest and in transit in large multi-site customer architectures where data is synchronised.
Holden says the alleged breach should serve as a warning for PoS vendors to harden their systems noting that hackers will breach businesses using the easiest path available.
"From my perspective, most hackers more often go along the path of least resistance and use the standard tools," Holden says.
"I think security should deter types of attacks, not types of attackers. In addition there must be better deterrents that would identify malicious changes in infrastructure and detect data loss." ®