This article is more than 1 year old
Hackers pop top 'secure' wireless keyboard and mouse kits, gain RCE
Patch? Nah, we'll just remove 'secure' from the tin: vendor
Ruxcon Wireless keyboard and mouse manufacturers including Microsoft, Fujitsu, and Logitech have been forced to fix borked encryption in peripherals that allow physical attackers to hijack computers.
Researchers and phDs Gerhard Klostermeier and Matthias Deeg with Germany-based security firm SySS tested five devices badged as secure including the Cherry AES B.Unlimited and Perixx Periduo-710W.
Klostermeier demonstrated to the Ruxcon hacking confab in Melbourne how each test subject permitted keystroke injection, mouse spoofing, replay attacks, and all but the Logitech set up had lax code protections.
The keyboard and mouse devices cannot be patched in existing products so four of the five vendors committed to fixing the bugs in newer editions.
Perixx did not respond to Klostermeier's and Deeg's private disclosures.
Cherry told the pair it will remove references to its product as secure instead of fixing the issues, and urged customers with high security requirements to use wired peripherals.
The remaining vendors played down some attacks and promised some fixes for upcoming products. Microsoft will fix replay attacks, will assess insufficient code protections, but will not shutter a mouse spoofing vector which it says is a feature, not a bug.
The duo wrapped the attacks into a tidy Raspberry Pi "Radio Hack Box" which could, if planted nearby, allow otherwise locked machines to be compromised.
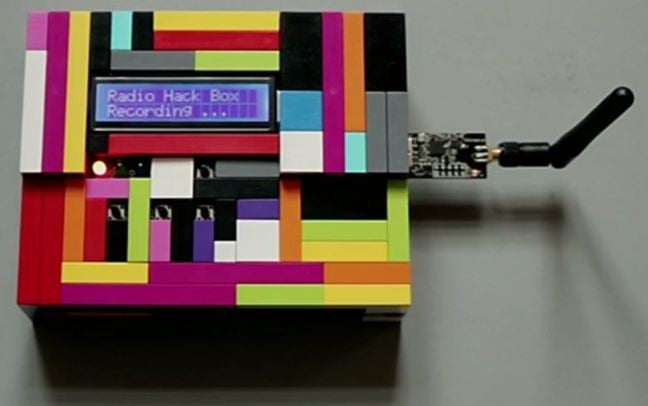
The Radio Hack Box prototype
It will allow attackers to spoof keyboard and mouse inputs for remote code execution, and use replay attacks to steal cleartext keystrokes so attackers can look for login credentials.
Klostermeier says the attack could be amplified with radio equipment to extend the keyboard and mouse attack from 15 metres to "several kilometres".
"You can exploit all of these vulnerabilities in real world attack scenarios," Klostermeier says.
"The normal distance is 10 to 15 metres but if you use software defined radio and apply some antenna you could extend it to several kilometres."
Klostermeier's and Deeg's attack uses an internal Python tool that inputs keystrokes into command using the inbuilt Windows virtual keyboard to run attack commands. It also uses with the Crazyradio PA USB device, and leverages Bastille's nrf research firmware to pull off the attacks.
The pair published a proof-of-concept video demonstrating the three-minute attack against the Microsoft Wireless Desktop 2000 which they say can be sped up to reduce time to compromise.
Their work joins efforts by internet-of-radio-things security company Bastille which in July hosed low-cost wireless keyboard and mouse setups through a bug it called KeySniffer. ®
