This article is more than 1 year old
Hacker's Icarus machine steals drones midflight
Popular RC protocol pwned
PacSec Security researcher Jonathan Andersson has developed a tidy hardware module capable of fully hijacking a variety of popular drones and remote control gear running over the most popular protocol.
Trend Micro's advanced security group manager told The Register he developed the Icarus box, and it only needs to be within range of a drone to hijack it with injected commands.
Any radio controlled device using the popular DSMx radio platform are affected.
These include drones manufactured by Walkera, AirTronics, and NineEagles, among many others.
Andersson demonstrated the hijack at the PacSec hacking conference in Japan yesterday.
"It's not a jamming system so i am not competing for control via RF power," Andersson told Vulture South.
"Full flight control is achieved with the target experiencing a complete loss of control -- it's a clean switch-over.
"The range of my proof of concept implementation is equal to a standard DSMx radio transmitter, though standard 2.4GHz ISM band amplification can be applied to extend the range."
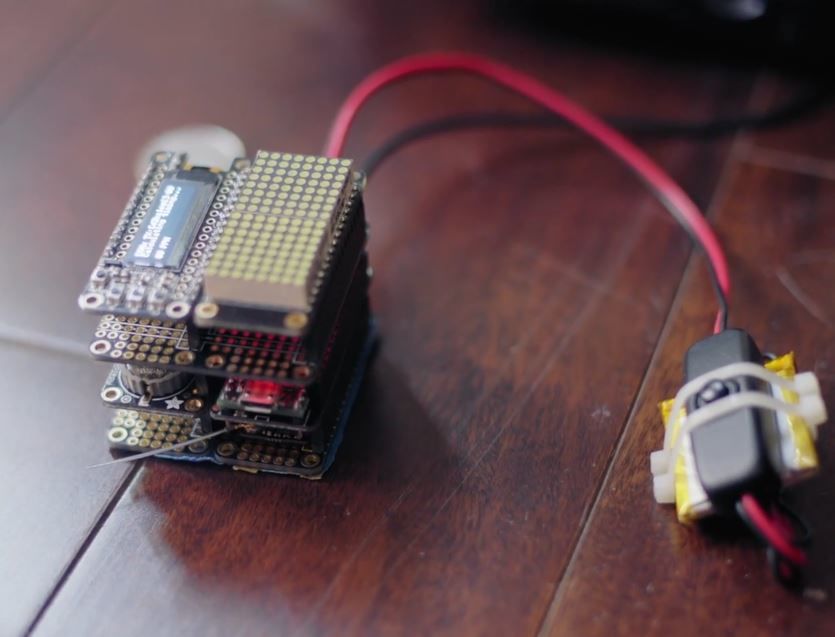
Icarus.
Andersson says Icarus determines the unique shared secret key within the DSMx binding process by observing the protocol and brute force.
This gives attackers complete control of the drone, while a timing attack which injects commands excludes victims from gaining control.
"It works against all DSMx based radio systems, which would include drones, airplanes, cars, boats, and so on," Andersson says.
The attack can likely only be fixed by updating receivers' firmware protocols, which is a feat not possible on most devices.
Andersson's slide deck is available for more information. ®
