This article is more than 1 year old
Hackers hustle to hassle un-patched Joomla! sites
If you didn't patch, you've probably been p0wned already
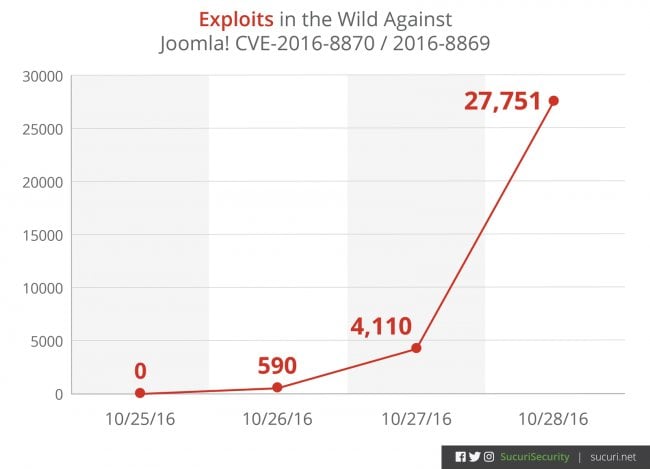
Attackers are already exploiting a dangerous privileged account creation hole in the Joomla! content management system attempting, with attempts made on about 30,000 sites in the days days after a patch for the flaw landed.
The vulnerability, which allows anyone to create privileged accounts on Joomla! sites, was first flagged in a scant Joomla! pre-release notice warning administrators to prepare for a then un-described but critical patch.
At the time The Register warned the then mysterious flaw would likely be exploited in the coming days and weeks as the respective patch is reverse-engineered.
Those attacks have eventuated faster than we predicted.
Sucuri analyst Daniel Cid says the attacks arrived in force three days after patching and were so large that any site that did not apply the patch has likely now been compromised.
"Less than 24 hours after the initial disclosure, we started to see tests and small pings on some of our honeypots trying to verify if this vulnerability was present," Cid says, adding attackers unsuccessfully targeted every Joomla site in Sucri's network.
"In less than 36 hours after the initial disclosure, we started to see mass exploit attempts across the web.
"In fact, because of the sharp increase, it's our belief that any Joomla! site that has not been updated is most likely already compromised."
Cid and colleagues were able to reverse-engineer the patch within a "few hours", creating an internal tool that could exploit the vulnerabilities (CVE-2016-8870, CVE-2016-8869) and upload backdoors to affected sites.
He says attackers begun immediately probing for user.register tasks and creating unauthorised users. Hours after IP addresses from Romania and Latvia begun mass scanning thousands of sites attempting to create the user db_cfg.
Joomla! has been downloaded more than 75 million times and runs on big ticket sites including McDonalds, Ikea, General Electric, Linux.com, and major news sites.
WordPress leads the open-source content management pack with some 140 million downloads.
"If you have not updated your Joomla site yet, you are likely already compromised," Cid says.
The engineer has detailed indicators of compromise that administrators can look forto determine if their Joomla! site was attacked. ®
