This article is more than 1 year old
Aw, snap: Independent disk drive failure rates from Backblaze
The good, the bad, and the ugly rusty spinners revealed
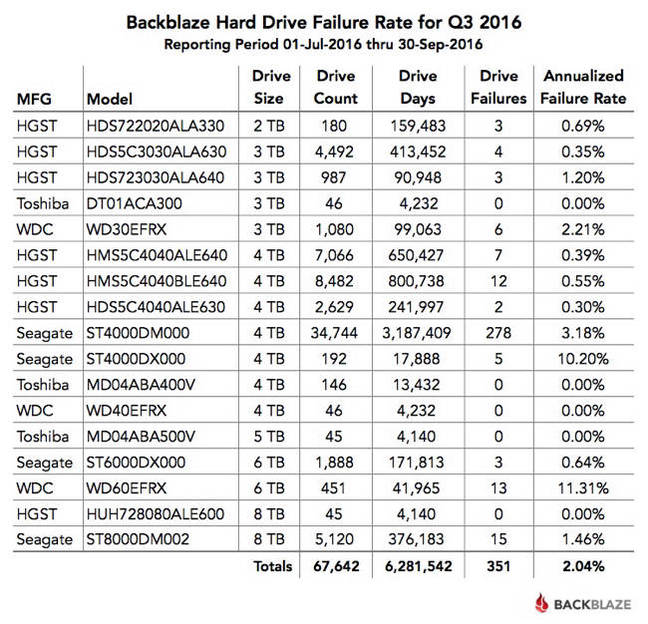
Backup and cloud storage provider Backblaze’s latest quarterly disk failure rate table shows WD 6TB drives had an 11.31 per cent annualised failure rate in the third 2016 quarter, with Seagate 4TB drives spinning into the ground almost as often, with a 10.2 per cent rate.
Having one in 10 or worse drive failure rates is not good, especially if you operate hundreds or even thousands of drives.
Backblaze is providing a great service by revealing its own experience of drive failures. We don’t get such rates from drive manufacturers.
Backblaze had 451 WDC WD60EFRX 6TB drives and 13 gave up the ghost. There were 192 Seagate 4TB ST4000DX000 drives and five went south. Toshiba drives were the overall best performer with zero failures.
Backblaze says its “annualised failure rate” is computed this way: [(Failures)/(Drive Days/365)] x 100. Here is Backblaze’s table of Q3 2016 disk failure rates providing this level of detail:
BackBlaze also calculates the annualised drive failure rate over the lifetime of each of the data drive models it currently has under management:
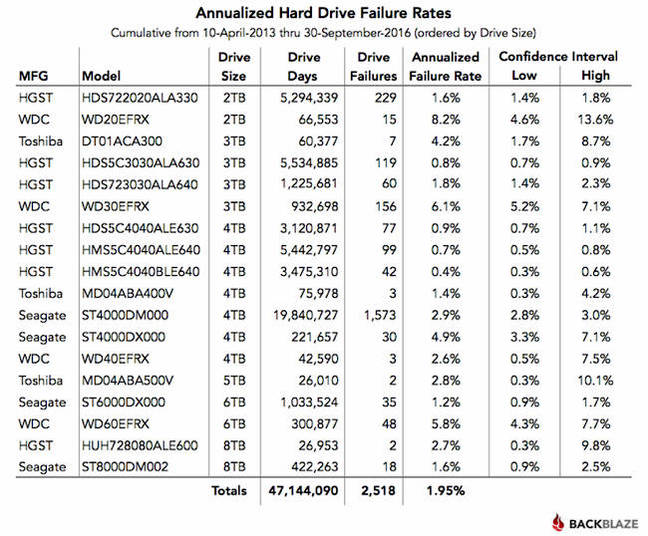
The WDC WD20EFRX 2TB drive has a woeful record, with the worst failure rate of 8.2 per cent, followed by its WD30EFRX 3TB product at 6.1 per cent. Third from the bottom is Seagate’s ST4000DX000 4TB drive with a 4.9 per cent failure rate.
The top performer is a 4TB HGST drive, the HMS5C4040BLE640 with a 0.4 per cent failure rate. Second best is another HGST 4TB drive, the HMS5C4040ALE640 at 0.7 per cent, and in third place is another HGST spinner, the HDS5C3030ALA630 3TB product at 0.8 per cent.
Backblaze has its test data published on a hard drive test data web page. Check it out to find out more about how reliable the drives it uses are. ®
