This article is more than 1 year old
Telegram API ransomware wrecked three weeks after launch
Crypto so bad that getting around it is shooting fish in a barrel
Ransomware scum abusing the protocol of the popular Telegram encrypted chat app have been wrecked and their malware ransom system decrypted.
TeleCrypt throws a message to Russian-speaking victims thanking them for helping the "Young Programmers Fund" via the US$78 (5000 ruble) ransom payments, a comparatively small charge compared to rival ransomware raiders.
Malware analyst Nathan Scott's work would be notably irritating for Telecrypt writers whose work was destroyed in the same month it was first noticed.
Scott says his decryption app exploits weaknesses in TeleCrypt encryption process allowing all files to be decrypted provided victims have an original good copy of at least one file.
"TeleCrypt uses the TeleGram API to send the information on its victims to the ransomware creator," Scott says.
"This way of the communication is very unique – it is one of the first to use a mainstream messaging client’s API, instead of a command and control server, to send commands and get information.
"Telecrypt encrypts files by looping through them a single byte at a time, and then simply adding a byte from the key in order - this simple encryption method allows a decryption application to be made."
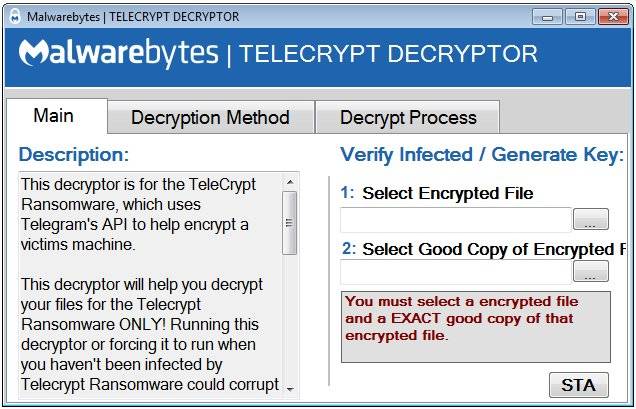
The Telecrypt decrypter.
Ransomware programs are falling like dominos as anti-malware researchers push harder.
Only yesterday ESET boffins bashed the Crysis ransomware releasing a tool to decrypt locked files.
Much of the security industry's fightback exploits encryption implementation errors, rather than problems with the math itself.
While solo efforts at ransomware disruption continue, many now take place under the umbrella of the NoMoreRansom Alliance which unifies the once-discrete but furious effort by malware researchers to lay ruin to scores of ransomware variants, leaving a scant few including the latest cryptxxx and cryptowall unbroken.
Criminals can net a conservative US$84,000 a month slinging ransomware for an investment of US$6000, a whopping 1425 per cent profit margin, Trustwave found last year. ®
