This article is more than 1 year old
Need Xmas ideas? Try CVE-2015-7645, a Flash gift that keeps on giving
Who the hell needs zero days?
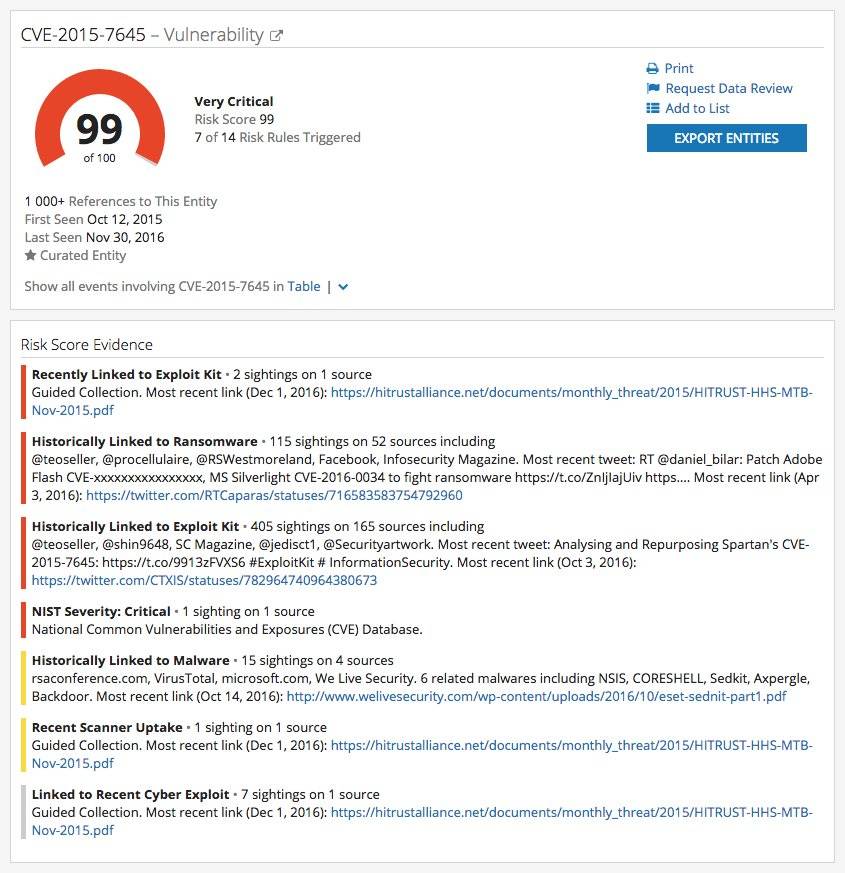
A Flash vulnerability subject to emergency patching by Adobe has been used in all major exploit kits to compromise users not already updated.
The vulnerability (CVE-2015-7645) patched in October last year was the first zero day since Adobe implemented more hardened security.
It was also the most pervasive among the vulnerabilities adopted by exploit kits, according to the Recorded Future study of an eye-watering 141 kits.
The once huge now dead Angler and Neutrino exploit kits used the flaw, along with popular hack boxes Magnitude, RIG, and Nuclear Pack, and challengers Spartan and Hunter.
"Adobe Flash Player's CVE-2015-7645 has been incorporated into seven exploit kits, the highest penetration level of our analysed vulnerabilities likely because it was the first zero-day discovered after significant Adobe security changes," researchers say.
"... it was quickly adopted as many other older exploits ceased working on machines with newer Flash versions.
"It impacts Windows, Mac, and Linux operating systems, which makes it extremely versatile."
The flaw was used in the operation Pawn Storm suspected Kremlin hacking operation.
Researchers say that the ease of exploitation and breadth of operating systems affected kept the Flash flaw in favour, despite Adobe's fast patch.
Adobe Flash remains the principal means of falling victim to exploit kits, and to that end Recorded Future recommends punting the ravaged runtime.
Google too wants Flash to dash having begun to debride itself of the internet relic
The team identified the Sundown exploit kit as the "rising star" in the underground with "significant adoption" among criminals.