This article is more than 1 year old
Go dark with the flow: Lavabit lives again
Another shot at spook-proofing email
It's taken longer than first expected, but the first fruits of Lavabit founder Ladar Levison's Dark Mail Technical Alliance have landed with the relaunch of the encrypted mail service he closed in 2013.
After shuttering Lavabit, Levison joined hands with Silent Circle to form the DMTA and promised Lavabit would flow again in 2014.
In 2015, Levison posted a GitHub repository putting forward a protocol to support fully “dark” email: the Dark Internet Mail Environment, or DIME, which has “multiple layers of key management and multiple layers of message encryption”.
The Libdime implementation offered both libraries and command line utilities, which is, after all, doing it the hard way: Lavabit Mark II puts that in the hands of users with the also-open-source Magma Webmail server implementation.
The Lavabit mail server, Magma first appeared on GitHub in 2016.
Levison writes “DIME provides multiple modes of security (Trustful, Cautious, & Paranoid) and is radically different from any other encrypted platform, solving security problems others neglect. DIME is the only automated, federated, encryption standard designed to work with different service providers while minimising the leakage of metadata without a centralised authority. DIME is end-to-end secure, yet flexible enough to allow users to continue using their email without a Ph.D. in cryptology.”
So what's in the protocol? Let's look at the specification, published here (PDF).
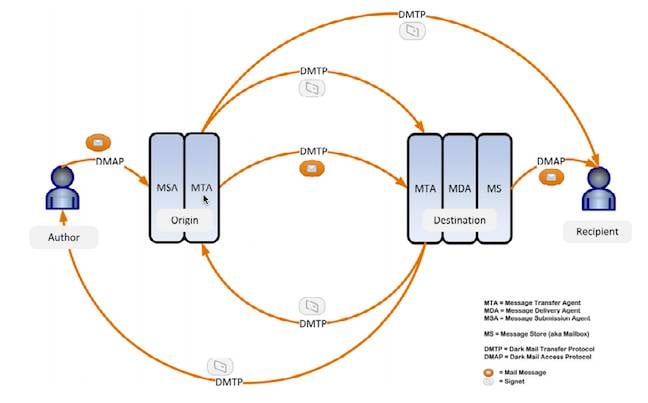
DIME's message flow. Image: The Dark Mail Technical Alliance
You don't get perfect security while you've still got wetware involved. The DIME document notes that if a user has a weak password or bad endpoint security, all bets are off.
Within that constraint, the DMTA says DIME's designed to provide “secure and reliable delivery of email, while providing for message confidentiality, tamper protection, and a dramatic reduction in the leakage of metadata to processing agents encountered along the delivery path”.
At the top level, the four components of the system architecture are email clients; privacy processing agents; key stores (with a resolver architecture to retrieve keys, in DIME called “signets”); and the encrypted message objects.
To most users, The Register will assume the only new concept here is the privacy processing agent (PPA). There are two kinds, the organisational PPA, and the user PPA.
The Organisation Privacy Agent (OPA) talks to both user email clients and the Internet at large, handling user key management to create “a secure transit channel that hides all information about the message using transport layer security”. It also “provides access to the envelope information needed for immediate handling.”
The User Privacy Agent (UPA) handles user-side crypto functions, and can reside in the user's email client or, in Webmail implementations, on the server.
DIME has three modes of operation:
- Trustful – the user trusts the server to handle privacy;
- Cautious – the server stores and synchs encrypted data, including encrypted copies of private keys and messages. Encryption can be carried out inside a user's browser;
- Paranoid – the server never sees a user's keys. There's no Webmail, and if you want to use multiple devices, it's up to you to synch them across different keyrings.
In technical terms, that means the system has to automate all aspects of key management; encrypt and sign messages without a user having to learn how to run it; and resist manipulation (including, ideally, even if a client is compromised.
The layering of encryption, the standard says, is designed to protect messages, even if (for example) a server along the way is compromised.
DIME relies on a concept of “signets” for keys: organisational signets, which are keys associated with a domain; and user signets, the key associated with an individual email address.
“The basic validation model is to obtain a signet from a credible primary source and then confirm it with another pre-authenticated source. The two pre-authenticated sources currently available are a management record signed using DNSSEC or a TLS certificate signed by a recognised Certificate Authority (CA). Both can be cryptographically traced by a signet resolver back to a trusted key that is shipped with the resolver.
As well as the Webmail version, Lavabit says it wants to develop clients for Windows, Mac OS and iOS, Linux and Android. ®
