This article is more than 1 year old
VMware to end support for third-party virtual switches
Virtzilla says hardly anyone isn't using its own vSwitches already
UPDATE VMware's let vSphere users know that it will end support for third-party virtual switches.
Virtual switches let you handle traffic generated by virtual machines. They've been a part of vSphere for years, because it just makes sense to have a virtual switch connect VMs rather than send traffic out of a host, into a physical switch, then back again.
VMware's early efforts in this field were modest. Cisco's Nexus 1000V, however, was better-regarded and reasonably widely adopted. IBM and HPE also have virtual switches.
Over the years, VMware's done better with its own efforts: the vSphere Distributed Switch is now considered to be a match for the Nexus 1000v. VMware also offers the VMware vSphere Standard Switch. There's also the Linux Foundation's Open vSwitch to play with.
A VMware spokesperson told us that the reason for the change is that few users bother with third-party virtual switches any more. “VMware’s native virtual switch implementation has become the de facto standard for greater than 99% of vSphere customers today,” the spokesperson said.
“This strategy is about investing in the priorities of our customers and simplifying the platform to create the best, most secure experience possible.”
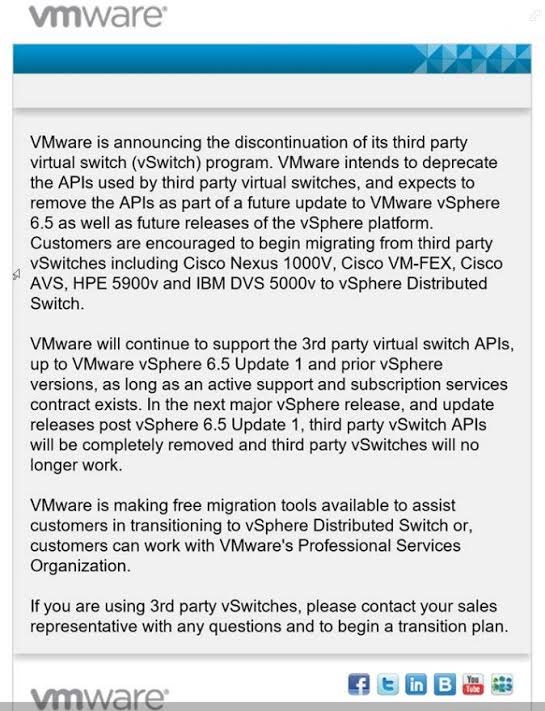
VMware's communiqué to third-party vSwitch users
This decision does also mean some pain for those running third-party virtual switches, as they'll have to migrate away from them whenever VMware does its next vSphere update. If current form holds, that will be some time next year.
Perhaps more significantly, this week has seen rumours emerge to the effect that Cisco is working on a release of iOS decoupled from hardware. If that rumour is true, it would set the cat among the pigeons if vSphere didn't play nice with future virtual versions of Cisco's various switches.
And then there's the issue of lock-in. A staffer from a hyperconverged systems vendor that supports multiple hypervisors, and who requested anonymity, believes some users may feel it is worth considering a multi-hypervisor strategy to ensure they're not tied to VMware's virtual switches. ®
UPDATE, MONDAY APRIL 3rd: Over the weekend, readers pointed us towards this knowledge base page offering more information on the decision to drop support for third-party vSwitches. Commenters also pointed out that some VCE products include the Nexus 1000v, meaning that one arm of Dell is asking its own customers to stop using software it once recommended! Cisco/NetApp Flexpods also included Cisco's vSwitch. Both VCE and FlexPods assume users follow a locked-down configuration of hardware and software. VMware's asking both to break those configurations.
