This article is more than 1 year old
Oh, great: There's a new Same Origin Policy exploit for Edge
Browser helps attackers by autocompleting passwords
Edge nemesis, security tester Manuel Caballero from Buenos Aires, has popped the browser again, getting around its Same Origin Policy to steal stored credentials.
Over at his Broken Browser blog, Caballero explains that an attacker can fake their originator for a referrer spoof, and “thanks to the existence of data-uris and the fact that most sites render iframes, we can end up turning this vulnerability into a full SOP bypass.”
It gets better: “Then, because the password manager tries to be smart and complete everything without checking too much, we can simply render a universal snippet of code that will work everywhere.”
He offers up a proof-of-concept (here) and if you want to see it but don't use Edge, there's a YouTube video:
Caballero explains:
We can force a window to change its location as if the initiator were the window itself. For example, a tab hosting evil.com can change the location of a Paypal tab to bankofamerica.com, then BankofAmerica will receive Paypal as its referrer instead of evil, because Edge confused the real initiator of the request. If we apply the same idea to iframes in the target page plus a data-uri with code, we can achieve a full SOP bypass.
Caballero reminds readers that he'd previously achieved an SOP bypass, but even if users had patched since then, the new attack will work.
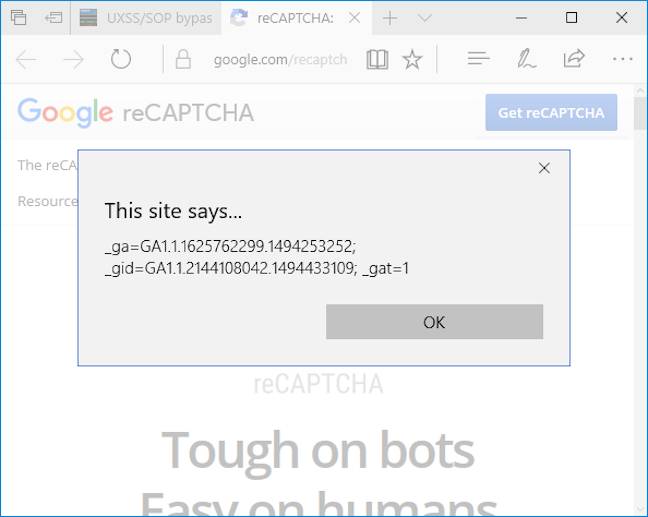
Want to grab someone's Google cookie? That works, too:
He explains how helpful Edge's auto-complete is with this code snippet:
<form> <input /> <input type="password" /> </form>
“That’s it! If we inject that code in domains with saved passwords, Edge will immediately autocomplete them”, he writes – so the following will show the password if you send the victim to Facebook:
<form> <input /> <input type="password" onchange="alert(this.value)" /> </form>
Patches will arrive soon or not, as Microsoft chooses.
Back in December, Caballero showed how a scammer could display legitimate-looking popups in Edge. ®
