This article is more than 1 year old
Dial S for SQLi: Now skiddies can order web attacks via text message
Katyusha scanner targets web servers with instant chat
Hackers are touting a tool that allows any idiot with a smartphone to conveniently order up mass SQL injection attacks against websites.
From what we can tell, you can either rent an instance of the crooks' Katyusha Scanner Pro for $200 per month, or install a copy on your own system for $500. This software uses the Anarchi Scanner, a freely available penetration testing tool, to perform SQLi attacks on websites. Crucially, it can be controlled via the Telegram instant messaging system.
So essentially, you run Katyusha on an internet-connected server, either rented or installed yourself, and then use Telegram to fire commands at it – such as attack somepoorbastard.biz or mydietpillsnotascam.org, and so on, until you hit a vulnerable site. Then, if you have the pro version, the package can automatically extract login credentials and extract the contents of internal databases. A light version of the scanner is available, too, if you think you can exploit any discovered bugs yourself.
This basically means non-tech-savvy criminals can easily book assaults against countless organizations and businesses from the comfort of their smartphones. It can be controlled via a web portal, we note, but it's pretty wild you can essentially text it orders via Telegram. Security researchers at threat intel firm Recorded Future found the package for sale inside one of the dark web's most exclusive and hidden hacker forums.
"While the hacking process could be controlled using a standard web interface, the unique functionality of Katyusha Scanner allows criminals to upload a list of websites of interest and launch the concurrent attack against several targets simultaneously, seamlessly controlling the operation via Telegram messenger," Recorded Future explains in a blog post.
The technology has garnered rave reviews from script kiddies as well as praise for a professional customer support operation. Of course, a seasoned cyber-crim could do all this from an SSH terminal on their smartphone or tablet; it's the fact that Katyusha is so easy to use is the mildly alarming thing about it.
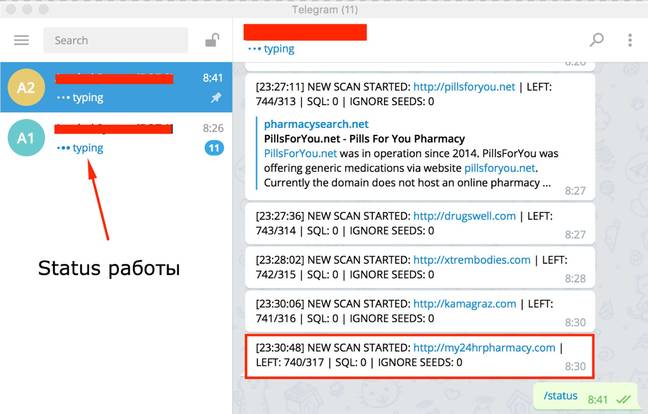
Attacks on demand ... A screenshot showing someone controlling Katyusha via Telegram messaging (click to enlarge)
Upon completion of the scan, Katyusha will display an Alexa web rating for each identified target, providing a handy guide to the potential significance and profitability of the discovered web security vulns.
"The availability of a highly robust and inexpensive tool such as Katyusha Scanner to online criminals with limited technical skills will only intensify the compromised data problem experienced by various businesses, highlighting the importance of regular infrastructure security audits," Recorded Future concludes.
The most widespread attacks in the first quarter of 2017 were SQLi and cross-site scripting, each accounting for about a third of the total number of detected attacks, according to a study by infosec outfit Positive Technologies. The report lists government agencies' web applications as the hackers' top target, followed by IT companies and financial organizations, and with educational institutions in fourth place. ®
Bootnote
The name Katyusha references an iconic multiple rocket launcher, developed by the Soviet Union during World War II and known for inflicting panic in Nazi forces with its stealthy and devastating attacks.
