This article is more than 1 year old
No one still thinks iOS is invulnerable to malware, right? Well, knock it off
As platform's popularity rose, so did its allure to miscreants
The comforting notion that iOS devices are immune to malicious code attacks has taken a knock following the release of a new study by mobile security firm Skycure.
Malicious mobile apps in Apple's App Store are mercifully rare (XcodeGhost aside) compared to the comparative "Wild West" of the Google Play store, which has come to exist despite the Chocolate Factory's best efforts to clamp down on the problem. However, hackers have found other ways to get malware installed, Skycure points out.
For one thing, Apple provides for sideloading apps as part of its support for enterprises and their proprietary business apps. But hackers have adopted social-engineering strategies to trick users into installing malicious apps through this route. Jailbroken iOS devices are more at risk of attack. Adware apps using approved certificates, malicious cables and the leveraging of vulnerabilities have also been exploited at times.
The number of iOS vulnerabilities patched in the first quarter of 2017 is already greater than the total number of iOS vulnerabilities discovered in all of 2016, according to Skycure. "Fortunately, Apple is still very fast at patching the OS and distributing updates," their report added.
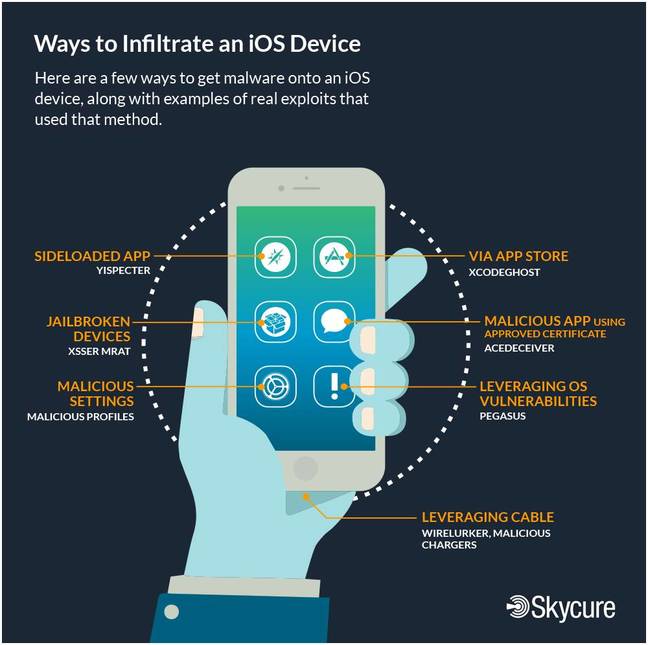
Ways to infiltrate an iOS device [source: Skycure blog post]
The study found that since iOS has become more popular as a platform, especially for enterprise executives and government agency officials, the rate of attacks and incidents of malware have increased. According to the report, the percentage of enterprise iOS devices that have malicious apps installed today has more than tripled since Q3 2016. In comparison, the rate of Android malware infections has stayed relatively flat.
Skycure declined The Register's requests to offer absolute figures for either the number of iOS vulnerabilities or frequency of iOS malware detections. Independent experts are sceptical about the angle taken by Skycure in its report.
"Android malware is still far more common," said Martijn Grooten, editor of industry journal Virus Bulletin. "The whole report looks like the authors are desperate to make iOS security sound as bad as possible."
The number of iOS nasties ever discovered is numbered in the scores. By contrast, Android malware runs into the millions and Windows nasties extend into the tens of millions. Skycure argues that despite the numeric insignificance of iOS nasties, they still need to be considered, not least because of the Bring Your Own Device (BYOD) trend.
Yair Amit, co-founder and CTO of Skycure, commented: "The iPhone ushered in the trend of BYOD, and the concept of apps and the app store, changing how IT manages corporate networks and equipment. The impact of iPhones and iPads on work productivity means more employees are choosing iOS devices for BYOD, and that makes iOS a valuable target for hackers.
"The number of vulnerabilities and malware does not indicate how secure a platform is, but it does indicate how often hackers are attempting to break into it."
Skycure's critical take on the security record of iOS, 10 years on from the creation of the mobile OS, can be found here. ®
