This article is more than 1 year old
Delphix dishes out Dynamic Data Platform with masking
Virtualises structured data for copies and cloud migration
Analysis Database copy virtualiser Delphix has relaunched itself as a Dynamic Data Platform supplier of personal virtualised data environments, covering on-premises and public cloud environments and masking out sensitive data.
Originally Delphix, founded in 2008, made a copy of structured data, such as an Oracle database, and provisioned virtual copies to test and dev and others who needed a database copy for their work. Such virtual copy provisioning was faster and more space efficient than making full-scale copies.
The funding history is:
- 2009 – $8.5m A-round
- 2010 – $11m B-round
- 2012 – $25m C-round
- 2015 – $75m D-round
That's a total of $119.5m.
Delphix bought Axis Technology in May 2015 and that provided the data masking technology.
CTO Adam Leaventhal left in February 2016. A new CEO, Chris Cooke, replaced founding CEO Jedidiah Yueh in April 2016, with Yueh becoming executive chairman.
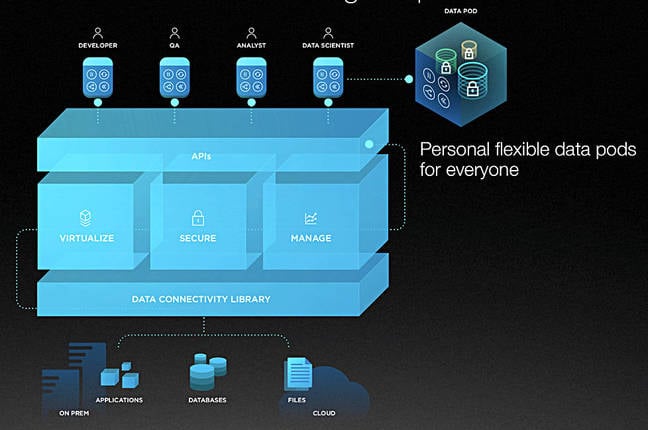
VP of engineering Eric Schrock became CTO in March this year, and now Delphix is relaunching itself with a refreshed exec roster and new marketing messages. The Delphix product portfolio is available as a seamless platform, the Dynamic Data Platform (DDP) offering, it says, which features virtualisation, security, management and self-service automation in one place. Data is moved and managed seamlessly – Delphix likes the word "seamless" – between source and target environments, whether on-premises, cloud, or hybrid – and quickly and securely provisioned where required.
It suggests that it is supplying a DataOps environment, sort of like DevOps, although you might think this is taking marketing a little further than it should.
In summary it seems as if the Delphix virtualisation engine now supports more source applications and can be extended to types of files. It runs as a virtual appliance on-premises or in the cloud and builds a metadata-based single repository as an abstraction above the source data stores, and can provision virtual copies of some or all of this data, with sensitive data masked out by the new masking engine.
Databases and apps
Essentially DDP runs as a virtual appliance and copies data from a set of sources – database data, file system data, and application binaries – into a kind of master data set, from which it can provision copies.
It is an efficient user of copy data space, SVP for products Patrick Lightbody explains, because: "The core technology is built on top of the ZFS file system, which gives us the ability to clone, branch, and snapshot data sets without taking any significant storage overhead. The result is that if you wanted to give 100 developers their own personal production instance to work with, you'd see nearly 100x storage savings with Delphix.
"Dedupe capabilities are inherit in the underlying ZFS filesystem, which allows us to make copies with zero additional storage overhead. Only when a user writes a unique data block to their copy is any additional storage consumed."
The Delphix Virtualisation Engine inside DDP is quite app-specific, as it has to understand the structure of each source application’s data store structure. It supports many databases: Oracle, DB2, AP ASE SQL Server, Postgres, and more*, plus multiple packaged and custom business applications: Oracle EBS, SAP and PeopleSoft, etc. SAP HANA support is in beta.
Files
The platform can handle any type of file, so long as it's in a file system that Delphix can connect to. NFS and iSCSI access protocols are supported.
Lightbody said: "We support connecting to particular folders and virtualising all files included. These are for Linux, Unix, and Windows systems. In addition to a long tail of custom files, we also have customers that take database backups from things like Postgres and MySQL and load them into our platform."
For applications: "We can provide data to applications, generically. This includes connecting to and providing active copies of data. In addition, as the application binaries are frequently needed with the data, Delphix supports virtualizing, versioning and provisioning the binaries alongside the data."
We're told: "Since Delphix provides active copies of data (predominantly databases), customers can use whatever BI tools are already in use. For example, customers have used Tableau and others against SQL-compliant databases. It's just a normal database connection to the downstream tools."
The DDP provides extensible support for arbitrary files, with Delphix providing "a toolkit such that customers, partners, or our services team can extend the file support. For example, to add scripts to load data into a non-supported database."
Pods and replication
Delphix POD scheme
The personal virtual data environments are called pods. Delphix claims these can be generated from multiple underlying data stores, giving users access to self-service capabilities to manage their data environments. They feature single-click refresh, point-in-time recovery, versioning, bookmarking and sharing.
The cloud
Supported clouds are AWS, Azure and the IBM cloud.
Data is replicated to the cloud in form by having a Delphix engine on-premises and in the target cloud. There has been an AMI of Delphix available to run in AWS for a little, and equivalent Azure support has just been added.
Can other clouds be supported? Lightbody said: "Because we are a virtual application, we can technically be deployed on almost any hypervisor platform. We've had customers deploy us in a wide range of places that we hadn't initially certified for (OpenStack)."
He says the replication "is our proprietary technology that we developed to deliver first time and on-going data changes (i.e., as a database is updated) across data centres, geographies, or clouds."
"Our replication technology... works with any data sources loaded onto our platform, giving you a consistent replication strategy regardless of underlying database vendor."
We're told customers moving data to the cloud can move massive amounts of data once but still refresh it, synchronise it, from on-premises or hybrid sources, which speeds up cloud adoption and operations.
Once data is in the cloud: "Customers can use the data however they would like, typically connecting to the data sources as regular connections (JDBC or ODBC)."
What about encryption? Lightbody said: "Our masking engine uses algorithms to do one way (masking) or reversible (tokenization) encryption of the data. These are applied as a customer determines is best."
Other copy data management products
How does Delphix compare to other copy data management products such as Actifio, Catalogic and Cohesity?
LIghtbody says: "They are one of a number of Copy Data Management (CDM) tools. None of them leverage something like ZFS (one of our core technologies), which gives us the ability to do filesystem snapshots.
"Instead those tools typically use the (infrequent) snapshots that come from the database itself. The result is that it takes much longer and more storage overhead to do all the things we just provide out of the box: refresh databases to the reflect the latest production data, reset the database state back to a point in time, or create branches of the database to match the branches of development.
"In addition to our virtualisation technology being a unique differentiator, the presence of our masking engine seamlessly integrated into our platform is a standout capability: nobody else in the CDM space or elsewhere [has it]. The result is that the data can be masked and cloned prior to leaving a secure data environment and then made available for a larger number of data consumers to use with little additional storage overhead."
Comment
Delphix was primarily a structured block-based data storage virtualiser and copier. This has been extended to covering less structured data in the sense of files.
Its technology is now simpler to obtain and offers something Delphix says is unique; personalised virtual (and masked) data environments for data consumers for faster application development, cloud migration and governance projects.
This is in data management territory, structured/unstructured data management territory. It differs from unstructured data management, as espoused by Rubrik and Cohesity, by not including data protection. There is also no analytics capability being mentioned and Delphix isn't talking (much) about business continuity and disaster recovery.
Yet Delphix is now set on a course that will bring it increasingly into competition with other data management players. It may hope that its structured data-handling capabilities will give it an edge over competitors lacking that. ®
*For each of the database families, there are OS, hardware, version and configuration options (e.g. Oracle Exadata, SQL Server Clustered, DB2 Blu, etc.) Delphix database product support details can be found here. Customers can connect to databases outside of the core Delphix support by integrating with toolkits and/or using the filesystem capability.
