This article is more than 1 year old
Apple iCloud Keychain easily slurped by cops, ElcomSoft claims
Credentials stored in the cloud succumb to forensic software
ElcomSoft, the Russia-based maker of forensic software, has managed to find a way for crime investigators to access the data stored in Apple's iCloud Keychain, if Apple ID account credentials are available.
Apple's iCloud Keychain is a remote copy of the password vault that's optionally available to users of iOS and macOS devices.
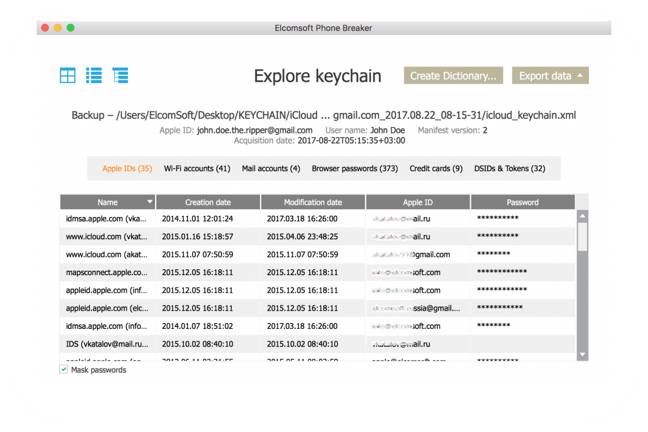
If enabled, it can store copies of credentials for Safari websites, for services like Facebook, Twitter and LinkedIn, and for applications like Calendar, Contacts, and Mail, along with credit card numbers and Wi-Fi network data.
It serves to replicate the contents of the device-specific Keychain database, which is exposed as an app to macOS users and as an API to developers on iOS devices. It also assists with two-factor authentication.
ElcomSoft's Phone Breaker 7.0 has gained the ability to access and decrypt iCloud Keychain data, under certain circumstances.
Users of Apple devices who have not enabled two-factor authentication and have not set up an iCloud Security code do not have an iCloud Keychain stored with Apple. Otherwise, the database exists in iCloud accounts, and can be accessed with an Apple ID, password, and – if the device is protected by two-factor authentication – a one-time security code.
In an email to The Register, CEO Vladimir Katalov said this capability is not the consequence of any vulnerability. Rather, it's intended for forensic investigators and law enforcement, given that an Apple ID and a trusted device are necessary.
Katalov said this is not a exploitation of a vulnerability and there's nothing Apple can patch. Rather, ElcomSoft is exposing functions that Apple has not made available – Apple does not provide any means of accessing iCloud Keychain.
Katalov said the technique works with beta releases of iOS 11 and macOS High Sierra, which Apple is expected to introduce in a month or two.
There's no security risk for Apple customers yet, according to Katalov. However, ElcomSoft is planning to implement the ability to access the iCloud Keychain with the help of an authentication token pulled from a PC or Mac.
"That way, that will be able to get just a couple of files from suspect's computer, and get all passwords and credit card numbers with no need to have anything else (credentials, trusted device etc), and with no traces left," he said.
ElcomSoft in February found that it was able to recover deleted Safari browsing history data from iCloud. In November 2016, the data harvesting biz discovered Apple's iCloud Drive was storing iPhone call logs without consent.
Apple's iCloud Keychain has elicited interest from security researchers because it's such a tempting target. In March, Apple fixed an iCloud Keychain vulnerability (CVE-2017-2448) that had been disclosed to the company by Alex Radocea, cofounder of Longterm Security, two months earlier.
Radocea elaborated on his findings in May and presented a more detailed account of his work at the Black Hat conference earlier this month.
An Apple spokesperson said the company was looking into ElcomSoft's claim, but did not respond further. ®