This article is more than 1 year old
SAP point-of-sale systems were totally hackable with $25 kit
Researchers able to hijack server and steal card details
Point-of-Sale systems from SAP had a vulnerability that allowed them to be hacked using a $25 Raspberry Pi or similar device, according to research unveiled at the Hack in the Box conference in Singapore last week.
Critical vulnerabilities in SAP's POS – since resolved – created a means for hackers not only to steal customers' card data but to gain unfettered control over the server, enabling them to change prices of goods with the help of a simple device, according to ERPScan.
SAP developed a patch after being alerted to the problem by ERPScan in April, allowing the enterprise app security specialists to go public with their discovery last week.
The root cause of the problem was that pre-patch SAP POS Xpress Server systems failed to perform any authentication checks for critical functionality that requires user identity. As a result, administrative and other privileged functions could be accessed without any authentication.
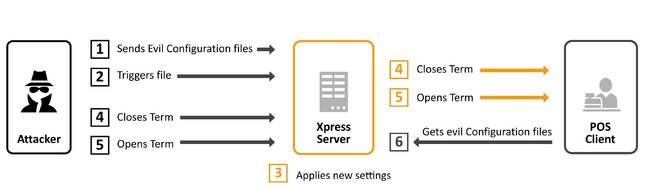
Attack scenario against SAP POS system [source: ERPScan blog post]
Left unpatched, the vulnerabilities would allow attackers to gain complete control of vulnerable systems, opening the door to espionage, fraud, and sabotage.
"The vulnerabilities enable remote starting and stopping POS terminals," ERPScan explains. "An attacker can remotely turn off all POS terminals within a merchant. Such DoS attack can be very costly for big retailers."
The exploit enables changing credit card number data masking so that all digits of a customer's card number will be printed on a receipt (prohibited by PCI-DSS, the credit card industry regulations). This information can be sent directly to a hacker's server – as shown in the clip below.
SAP POS is client-server technology that forms part of the SAP for Retail line-up. The technology is used by 80 per cent of the retailers in the Forbes Global 2000.
"Broadly speaking, it's not a problem of SAP. Many POS systems have similar architecture and thus same vulnerabilities," said Dmitry Chastuhin, one of the researchers who identified the vulnerabilities. "So, once an attacker is in the network, he or she gains full control of the system, including prices and credit card data. That's unbelievable how woefully insecure we are when just swiping a card."
In a statement, SAP confirmed the issue and urged customers to patch their POS systems, if they hadn't done so already.
SAP Product Security Response Team collaborates frequently with research companies like ERPScan to ensure a responsible disclosure of vulnerabilities. All vulnerabilities in question in SAP Point of Sale (POS) Retail Xpress Server have been fixed, and security patches are available for download on the SAP Support Portal. We strongly advise our customers to secure their SAP landscape by applying the available security patches from the SAP Support Portal immediately.
®
