This article is more than 1 year old
Sir, you're doing 60 in a 30mph container zone. What are you, some kind of devops cop?
Well... we prefer containerised app info highway code
Profile An Israeli startup has devised a containerised traffic cop which it claims stops rogue containers from misbehaving at run-time.
Aqua Security uses a combination of intelligent defaults, machine learning, and threat research to provide life cycle security for container-based applications. it supports both Linux and Windows containers, multiple orchestration environments, both on-premises deployments as well as on AWS, Azure and other public clouds.
Its container security product has a specialised Enforcer container slipped between the Docker engine and the other containers running in a micro-services system. It enforces a whitelisting approach to stop wrong-doings, snooping on the run-time containers and policing their behaviour, trapping rogue containers.
How does this work?
It is part of Aqua's Container Security Platform. This starts its work in the devops environment where code is issued to a registry several times a week with none of the six month release cycle formal checks that are the case with legacy software. This is a continuous rather than stepwise release cycle.
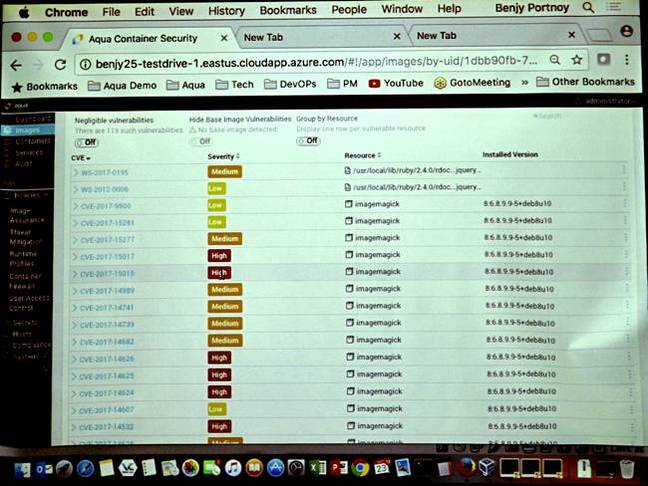
The individual developers have to implement security facilities and needs helping and policing. Aqua provides services at build time and can fail builds, flagging container vulnerabilities, and making suggestions where it can as to how they can be fixed by the developer.
If the developer ignores this and pushes a vulnerable image into the registry, then it will run. That's where the firm claims Aqua Enforcer comes in, catching the rogues. It's lightweight and uses negligible host server resources, the company claimed.
Aqua says that traditional security or code inspection tools can't see containers, they only get calls from the Docker Engine acting on behalf of containers.
With virtual servers VMs are less fluid than containers and have the same IP address day to day. Static tools have developed as has NSX-y stuff so they can see actions/events/calls from the VMs.
But with a container you never know what the IP address will be at run time. To bypass this limitation, the Enforcer monitors the services called by a container, not its IP address.
The Enforcer also implements a kind of machine learning and also records any run-time container activities and builds a profile. If in future the container deviates from this profile then the deviating action can be denied and the attempt logged.
Instead of an entire application being shut down only a misbehaving container part is trapped with the rest of the application continuing, which ought to minimise disruption to the application users.
Aqua background
Aqua was founded in 2015 by CEO Dror Davidoff and CTO Amir Jerbi. It raised $4.5m in seed funding in the founding year, $9m in 2016 and $25m this year. There are R&D offices in Tel Aviv with sales and marketing offices in Boston and San Francisco. It's operating in Europe via partners.
Customer numbers are in double figures, with a number of marquee accounts such as a top 10 software company and a top five insurance supplier. It supports Docker and Kubernetes, and container deployment on Windows and Linux.
Competitors include Twistlock and Capsule8. Aqua reckons its overall approach controls vulnerabilities in the software development pipeline and at runtime. ®