This article is more than 1 year old
What do Vegas hookers, Colombian government, and 30,000 other sites have in common? Crypto-jacking miners
Someone’s potentially getting rich – and it isn’t you
Over the past few months there has been an alarming rise in the number of websites running code that silently joyrides computers and secretly makes them mine digital currency for miscreants.
The latest count suggests more than 30,000 sites are quietly running JavaScript miners on people's PCs and handhelds – way more than previously thought.
An analysis, published this month by infosec guru Troy Mursch, revealed that the vast majority of currency-mining software came from Coinhive, the freely available JavaScript code developed to mine Monero. It appears the scripts were slipped into most, but not all, webpages covertly by hackers and other miscreants. In all, Mursch found 30,611 sites on the web running Coinhive's JavaScript to effectively crypto-jack machines into digging up digital dosh for shady netizens.
For example, DNS provider ZoneEdit was running Coinhive code on 324 parked web domains: on Monday this week, the biz coughed up to the sneaky inclusion and removed the software. Las Vegas ladies of the night were also mining crypto-currency on punters' PCs. A Colombian government agency's website was hijacked to covertly craft coins. A parody website was even created to "warm" your MacBook as winter approaches: obviously, it was running a miner.
While a few sites chose to deliberately run Coinhive's JavaScript – such as ZoneEdit and the Pirate Bay – the number of websites unwittingly running the software, inserted by persons unknown without permission, is much higher. We've already seen organizations from UFC to CBS's Showtime running Coinhive's miner inadvertently. This latest scan by Mursch revealed Papa John's Pizza in Mexico and the US National Association of Doctors were harvesting Monero, neither of which are likely to have installed it deliberately. Earlier this month, Papa John's in Ecuador was also pwned to run Coinhive code on its site.
In addition, it appears that many of these mining operations are being run by one person. Mursch found that one “Mohammad Khezri” of Iran seems to be controlling a vast number of mining operations spread across many domains to maximize his returns.
Naturally not many people are wild about contributing their power and CPU cycles to make strangers money. Antivirus packages and ad blockers now actively shut down Coin Hive's code in browsers. The miner's programmers are fine with that, and have stopped developing the software in favor of AuthedMine, which asks people's permission before mining – however, the original sneaky code is still the go-to miner of choice for online crims.
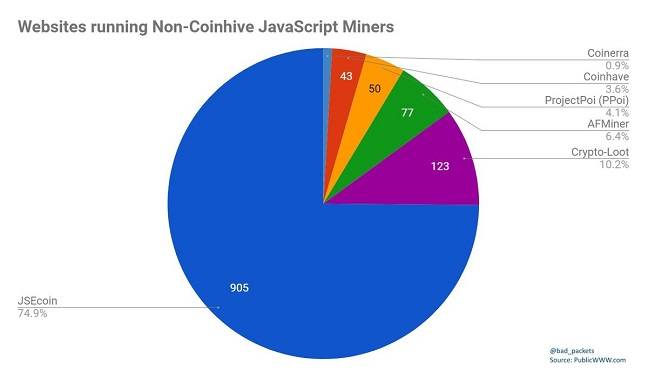
There are alternatives, such as JSECoin, that are being picked up by site owners and scumbags.
"Coinhive is not the only JavaScript miner available for crypto-jacking use," Mursch said. "Many competitors have popped up in its wake. Using PublicWWW, I found JSECoin was in a distant second place behind Coin Hive on 905 websites."
In the meantime, Mursch has urged Google engineers to add some kind of mechanism to Chrome that can halt alt-coin miners. While there's nothing wrong with informed and careful use of coin-mining software on webpages – it is supposed to be an alternative way for webmasters to earn money besides adverts – the quickly increasing scale of crypto-jacking suggests that such blocking measures will have to be taken in browsers to curb the menace of CPU-cycle thieves. ®