This article is more than 1 year old
That $10,000 Facebook bug: Photos shafted, addicts screwed by polls
Strangers' snaps glimpsed, deleted with code you wouldn't touch with a ten-foot poll
A security researcher found a way to delete any picture on Facebook, irrespective of whether it's public or private, by cunning use of polls.
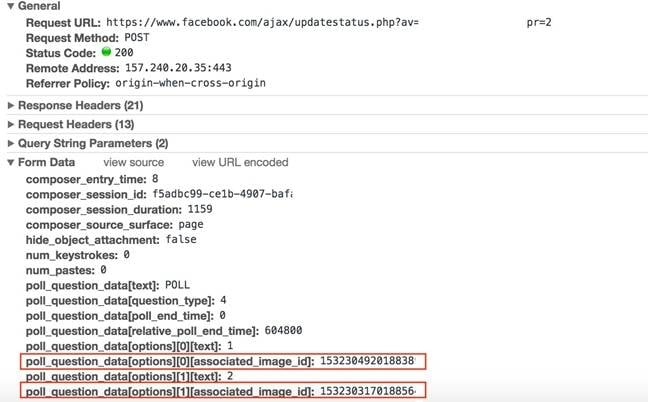
Pouya Daribi was digging around in the software used by Facebook users to set up quick opinion polls on their profile pages. When creating these informal surveys, the social media addicts can select photos to appear alongside the questions, and the ID codes for these pictures are embedded in the HTML form submitted to Facebook's servers.
You can see where this is going. By jiggering around with the parameters in the request, Darabi found he could attach any image by changing the ID numbers. This allowed him to preview pictures uploaded online by strangers, and add them to a poll, and when he deleted that poll, the attached images were permanently deleted from the social network as well.
The vulnerability is not quite as trivial as it appears: the ID numbers are not entirely sequential for pictures so a miscreant would have to feel their way through in the dark until they hit a valid image. It would be difficult to exploit it in a targeted way, however for causing general mischief it would be perfect. Discovering and reporting the security blunder earned Darabi a $10,000 award from Facebook's bug bounty program.
The researcher's writeup, published on Saturday, has some encouraging news as to how quickly Facebook fixed the issue. Darabi alerted the website's security team, along with a proof of concept, on November 3, and within 12 hours Facebook had triaged the problem and rolled out a full fix two days later.
Facebook added the poll feature earlier this month, so it's likely there are other flaws waiting to be found and dealt with. Given the money Facebook is offering, it's time to get digging and see. ®