This article is more than 1 year old
Merry Xmas, fellow code nerds: Avast open-sources decompiler
RetDec will turn binaries into something more legible
Malware hunting biz and nautical jargon Avast has released its machine-code decompiler RetDec as open source, in the hope of arming like-minded haters of bad bytes and other technically inclined sorts with better analytical tools.
As discussed as the recent Botconf 2017 in France earlier this month, RetDec provides a way to turn machine code – binary executables – back into an approximation of the original source code.
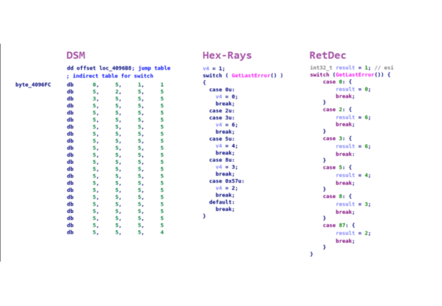
Where disassemblers convert binaries into assembly code – a somewhat readable representation of machine code – decompilers attempt to go back further to a higher-level source code language not tied to a specific processor – something more readable like C code.
Avast has used RetDec, which is based on LLVM, to decompile various ransomware strains, such as Apocalypse, BadBlock, Bart, CrySiS, TeslaCrypt, and others, in order to undo the unwanted encryption of victim's files.
In an email to The Register, Jakub Kroustek, threat intelligence team lead at Avast, said that while there are a variety of good decompilation tools available, many are paid products and cannot easily be extended.
Existing open-source decompilers provide an alternative, he said, "but these do not always achieve proper stability, code readability and quality."
Kroustek said he hopes RetDec, offered under a friendly MIT license, "will fill a gap in the market, in terms of produced code quality and [extensibility]."
He expects RetDec will be helpful not only to security researchers but to developers who are interested in studying how their code compiled and those working on reverse engineering projects.
RetDec stands for Retargetable Decompiler, meaning it can be used to target code from different 32-bit architectures – Intel x86, ARM, MIPS, PIC32, and PowerPC – in various formats – ELF, PE, Mach-O, COFF, AR (archive), Intel HEX, and raw machine code.
As a machine-code decompiler, RetDec is not suited for decompiling bytecode derived from Java, Python, or .Net source files.
Because the code compilation process jettisons useful information, reversing the process tends to fall short of the original, like compressing an image with a lossy algorithm and then re-enlarging it.
Decompilation may be made more difficult still if the writer of the code attempts to obfuscate it.
RetDec, available as an online service since 2015, attempts to address these challenges by utilizing debugging information and reconstructing instruction idioms, among other techniques.
"Our motivation is to contribute back to the security community, [whose] tools we are using on daily basis – so why not to share back also our own tools?" said Kroustek. "Secondly, we hope that involvement of more users and developers will further improve our tool."
Kroustek said in the four days since the code has been available, Avast has already received dozens of messages, improvements, and bug reports. ®
