This article is more than 1 year old
Apple's top-secret iBoot firmware source code spills onto GitHub for some insane reason
If you want a crash course in learning Arm code, now's your – hm, maybe not
The confidential source code to Apple's iBoot firmware in iPhones, iPads and other iOS devices has leaked into a public GitHub repo.
The closed-source code is top-secret, proprietary, copyright Apple, and yet has been quietly doing the rounds between security researchers and device jailbreakers on Reddit for four or so months, if not longer. Where exactly it came from, no one is sure for now.
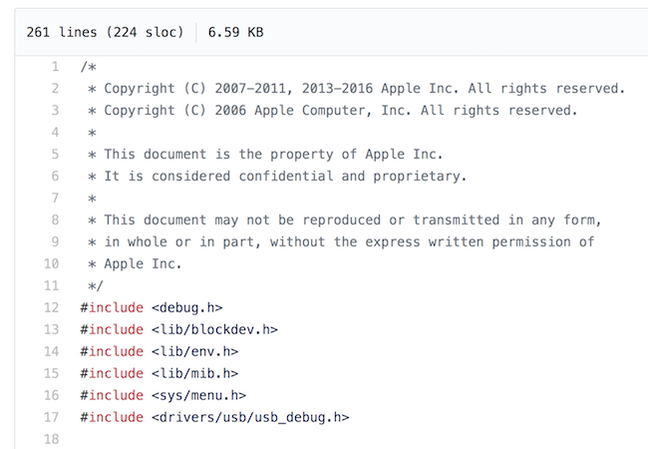
Screenshot of the leaked code ... Hands off, says Apple
Crucially, within the past day or so, someone decided to dump a copy of this secret sauce on popular developer hangout GitHub for all to find. Links to the files began circulating on Twitter in the past few hours.
The source was swiftly taken down following a DMCA complaint by Apple, which means the code must be legit or else Cupertino would have no grounds to strip it from the website. However, at least one clone of the software blueprints has remerged on GitHub, meaning you can find it if you look hard enough.
Fun thing about the DMCA: it required Apple to state, under penalty of perjury, that the iBoot source code was legit: https://t.co/PKHZqcEe6h
— Karl (@supersat) February 8, 2018
We're not going to link to it. Also, downloading it is not recommended. Just remember what happened when people shared or sold copies of the stolen Microsoft Windows 2000 source code back in the day.
According to those who have looked through the leaked iBoot source, the blueprints look legit. They include low-level system code written in 32 and 64-bit Arm assembly, drivers, internal documentation, operating system utilities, build tools, and more. Every file of the code is marked "this document is the property of Apple Inc," and: "It is considered confidential and proprietary. This document may not be reproduced or transmitted in any form, in whole or in part, without the express written permission of Apple Inc."
iBoot is a second-stage bootloader that's responsible for providing iOS's Recovery Mode to fix kit that gets screwed up. It runs on-screen, and over a physical USB or serial interface. When not in the recovery position, it verifies that a legit build of iOS is present, and if so, it starts up the software when the iThing is powered on or rebooted. The bootloader is highly protected, is stored in an encrypted form on devices, and is key to maintaining the integrity of the operating system.
It can be abused to jailbreak iOS devices to install unofficial customizations and applications. Thus, releasing the source code does not put people directly at risk – it simply makes it easier for folks to find exploitable bugs, and leverage them to hijack iBoot and jailbreak iThings.
Specifically, what we're talking about here is the source code to iOS 9's iBoot, which was first released in 2015, although some of the files have a 2016 date in them. How this affects today's devices running the latest software is unclear – some parts of the code may possibly linger on in iOS 11. No cryptographic keys or secrets have been found so far in the spilled documents.
For now, don't panic.
No one's going to hack your iPhone or iPad over the air, nor via a webpage or an app, from this leak. The code is useful for the tight-knit crowd of eggheads who like rummaging through firmware code looking for holes to exploit to jailbreak devices using a tethered physical connection to a computer. Apple has recently-ish stepped up its security, with its secure coprocessors and other measures, to thwart jailbreaks. Perhaps now fans will be able to find new ways to jailbreak and customize their iGear, now the blueprints for the bootloader are sitting on the internet in plain sight.
Instead, we recommend you just sit back, relax, and marvel at how Apple somehow managed to lose control of such a central, critical and hush-hush component of its software stack. And wonder what else has leaked from Cupertino's highly secretive idiot-tax operations.
Apple could not be reached for immediate comment. ®

