This article is more than 1 year old
Running Drupal? You need to patch, patch, patch right now!
Website building biz warns exploit may come in hours
Anyone running a website built with Drupal should stop whatever they are doing right now and install critical security patches.
The organization behind the open-source software today put out an urgent security patch to address a remote code execution vulnerability in "multiple subsystems" of its content management system software.
The holes could allow hackers to attack a Drupal-powered website in a number of different ways and that "could result in the site being completely compromised." In other words, it's really bad.
A hacker will be able to hack your site from any webpage, the Drupal project warned, and it doesn't require them to login or have any privileges, meaning that a completely anonymous miscreant can take over your vulnerable site as well as access, delete, and change non-public data.
There is no attack code circulating in the wild right now, but the Drupal bods have warned it could be a mere matter of hours before some is developed. Which means one thing: patch. And do it now.
So what's the problem?
The flaws – designated CVE-2018-7600 – are in the software's core, and affect versions 6, 7 and 8 of its content management software.
Drupal's makers are so concerned that malicious actors will be able to develop attack code fast that it took the rare step of tipping off website administrators last week that important fixes were incoming so the web admins could schedule downtime.
Drupal has also produced patches for older versions of its latest software – 8.3 and 8.4 as well as the most current 8.5 version – to ensure that websites can be updated as soon as possible, rather than require an overall update. A 7.x patch is also available.
"The Drupal Security Team urges you to reserve time for core updates because exploits might be developed within hours or days," it warned last week.
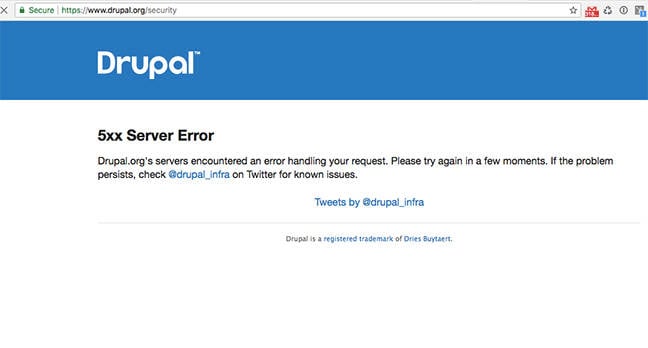
While the approach of giving website administrators a heads-up – including a window of 6pm to 7.30pm UTC – was good in theory, it backfired somewhat on Wednesday when the huge focus of attention ended up overwhelming the project's servers, making it harder for it to publish and disseminate the actual patches and further information.
As administrators waited patiently – and impatiently – for the patches to drop, an impromptu series of conversations started up on mailing lists and on social media. A game of internet hangman popped up. Memes erupted.
It may be worth noting that while a critical vulnerability in one of the world's most popular content management system is not a good thing, it can have interesting side-effects: such as when the website of law firm Mossack Fonseca was hacked and ransacked, providing the extraordinary information that led to the so-called Panama Papers – all because it failed to update Drupal and so patch a critical vulnerability.
The Panama Papers revealed a vast global conspiracy to hide money in overseas bank accounts and resulted in unprecedented promises to cut down on tax evasion.
We'll have to wait and see if anything similar emerges from this security scramble. ®
PS: If you're still on Drupal 6, an unofficial patch is available here.