This article is more than 1 year old
Uh-oh. Boffins say most Android apps can slurp your screen – and you wouldn't even know it
Fancy that
What is billed as the "first large-scale empirical study of media permissions and leaks from Android apps" has found that an alarming number can help themselves to your screen.
Over 89 per cent of apps in the Google Play store make use of an API that requests screen capture or recording – and the user is oblivious as it evades the Android permission framework.
"Our study reveals several alarming privacy risks in the Android app ecosystem, including apps that over-provision their media permissions and apps that share image and video data with other parties in unexpected ways, without user knowledge or consent," the authors note.
"We also identify a previously unreported privacy risk that arises from third-party libraries that record and upload screenshots and videos of the screen without informing the user and without requiring any permissions."
Authors Elleen Pan (Northeastern University), Jingjing Ren (Northeastern University), Martina Lindorfer (UC Santa Barbara), Christo Wilson (Northeastern University), and David Choffnes (Northeastern University) studied 17,260 apps over a year from Google Play Store and other download sites, and used dynamic analysis on a subset of around 9,000 apps. Their paper is titled Panoptispy: Characterizing Audio and Video Exfiltration from Android Applications (summary and PDF).
They found that users and app developers, who purportedly set and control permissions, are unaware what third libraries are slurping. Or, in their words, the permission model is flawed because it's a) "coarse grained" and b) "incomplete".
There's a gaping void in Android security. "There is no permission required for third-party code in an app to continuously record the screen displayed to the user," they note.
Google captured over 80 per cent of the market by giving away Android for free, allowing it to dominate search, maps, video and more. But Google's main business is consumer data processing, selling the forensic targeting of users to advertisers. The more a phone knows, the more targeted and effective its ads can be.
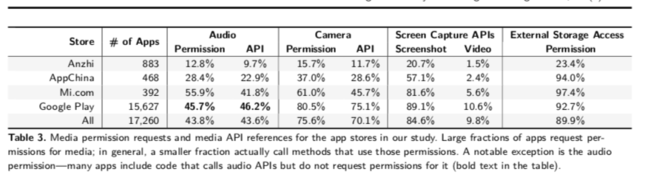
Source: Panoptispy: Characterizing Audio and Video Exfiltration from Android Applications; Pan et al (click to enlarge)
On the upside, the authors "uncovered few instances of covert recording (ie, apps taking pictures or videos without users intentionally doing so)".
But they admit they may have missed a few as native code is not analysed. "Our static analysis approach focuses on methods from the Android SDK and not native code, so we may miss cases of media leaks. Likewise, we may miss leaks from dynamically loaded code."
The researchers plan to investigate third-party libraries on iOS next to see what slurping may be taking place there. ®
