This article is more than 1 year old
HTTPS crypto-shame: TV Licensing website pulled offline
Telly taxpayers' info sent in the clear
The UK's TV Licensing agency has taken its website offline "as a precaution" after being blasted for running transactional pages that were not sent over HTTPS.
The publicly funded outfit had been criticised for inviting folk to submit sensitive data over unencrypted links. Just a few hours after proclaiming "we will soon migrate our entire website to HTTPS" it announced:
We are having issues with the TV licensing website, and we will restore the website as soon as we can.
— TV Licensing (@tvlicensing) 5 September 2018
The telly taxman has been maintaining a secure version of its website but it also ran an HTTP branch – which crucially didn't redirect over to HTTPS even for handling forms containing sensitive personal information.
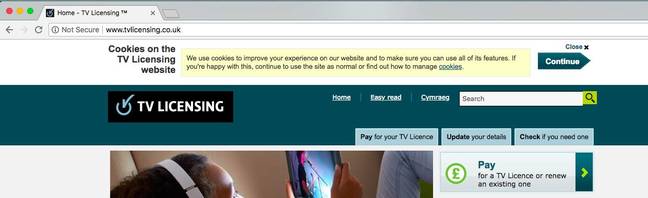
Following changes it made in late July, Google Chrome began clearly marking the HTTP version of the website as "Not Secure". Despite the HTTPS-everywhere push, the authority supports a website where data is exchanged without encryption and even goes out of its way to ensure this version appears first in search engine listings.
Yesterday, the form for submitting a name and email address through the site – step one for applying for a TV licence – was not secure. The form for home addresses wasn't either. Worse still, as of Wednesday 5 September, the form for submitting bank details for setting up a direct debit was also insecure.
"It's HTTP through the whole thing. Name, address, email, and bank details," infosec consultant Scott Helme sighed on Twitter. "They do card payments over HTTPS but only because it's an external provider."
Techie Mark Cook let tvlicensing.co.uk know via Twitter. He sent screenshots of the insecure connection process and later blogged about his concerns.
After some prodding, TV Licensing told Cook that all was well, advising him to ignore any warning from Chrome. "Our website is secure and security certificates are up to date. Pages where customers enter data are HTTPS. Non-HTTPS pages are safe to use despite messages from some browsers (e.g. Chrome) that say they are not."
TV Licensing told El Reg that herding consumers towards unencrypted transactional pages was a slip-up it was correcting:
We take security very seriously which is why we use encryption for all payment transactions. However, an issue has been brought to our attention over the recent level of security on transactional pages which were previously fully secure via HTTPS, and as a precaution, we have taken the website offline until this is resolved and are working urgently to fix it. We've identified that this issue has happened very recently, and we're not aware of anyone's data being compromised.
TV or not TV, that is the question
As Cook blogged: "The most common misconception is that secure HTTPS connections are only required on pages that are highly sensitive, such as processing payments. The UK's National Cyber Security Centre advises that all websites should use HTTPS, 'even if they don't include private content, sign-in pages, or credit card details'."
Running an unencrypted site means hackers might be able to snoop on traffic or inject code into its pages, perhaps via a man-in-the-middle attack or similar.
TV Licensing does have a secure version of their website, "it's just that you need to manually type in the 's' after the http, which is of course ridiculous," Cook said. "The TV Licensing website specifically tells search engines to use the insecure version over the secure version by using a canonical tag."
Cook's concerns could be addressed by TV Licensing dropping its odd search engine preferences alongside adding a few lines of code to redirect all HTTP requests to HTTPS.
TV Licensing customer support said on Wednesday, soon after replying to Cook, that it would "soon migrate our entire website to HTTPS", acknowledging the arguments of Cook and others. Just hours later, the site was taken offline and is still not back up, though the error page is on HTTPS.
Cook said: "I'm really glad that tvlicensing are taking steps to make their website more secure. My post was written after tvlicensing.co.uk had publicly responded on Twitter, saying their website was secure... [which] suggested at the time they were going to take no action. It's good to hear that it was a temporary glitch, but it would be reassuring to know exactly what time frame this was over and what tvlicensing.co.uk's estimate of potentially affected customers is."
Infosecurity consultant Paul Moore commented: "There really are no words for such ineptitude, but at least they're moving to HTTPS everywhere as a result of this." ®
Bootnote
A shout-out to readers Paul R and William B who expressed concerns that the connection to TV Licensing's website was untrusted late last year. Their hackles were raised by warnings generated through Firefox, related to TV licence renewal emails. The Google Chrome warnings – along with Cook's blog post – appear to have brought a long-simmering issue to the boil.