This article is more than 1 year old
Cloudflare invites folk to dabble in the 'distributed web' with InterPlanetary File System gateway
Five billion pages on open-source project, just like the original World Wide Web
Cloudflare has decided the four-year-old InterPlanetary File System (IPFS) project looks strong enough to warrant a little love, and has launched a gateway to allow the IPFS-curious to try out the "distributed web" protocol.
The hosting outfit said users can use IPFS both to find and host content (noting there are currently about five billion pages of IPFS content) without installing and configuring their own client software.
The company explained in a blog post that, as a distributed file system, IPFS has a couple of advantages over HTTP/S: users can host content themselves without big hosts as gatekeepers (just like the original vision for the web, really), and because the address unit is content rather than a host's location, it's resilient against outages at particular hosts.
IPFS borrows its content-addressability from the Bitcoin and BitTorrent protocols. Like BitTorrent, all participants in the network (as Cloudflare put it, from a Raspberry Pi to "the world's biggest server") store and serve blobs of content and, like Bitcoin, content is addressed by its hash.
Cloudflare said: "Rather than asking the network 'get me the content stored at 93.184.216.34,' you ask 'get me the content that has a hash value of QmXnnyufdzAWL5CqZ2RnSNgPbvCc1ALT73s6epPrRnZ1Xy.' (QmXnnyufdzAWL5CqZ2RnSNgPbvCc1ALT73s6epPrRnZ1Xy happens to be the hash of a .txt file containing the string 'I'm trying out IPFS')."
IPFS addresses, Cloudflare said, are multihashes – they carry information about the hashing algorithm and hash length used (the leading "Qm" in the example indicates SHA-256) as well as the the hash output.
The hashing also protects data from being interfered with in transit, since any alteration to the file will show up when you test the received content's hash against the requested hash.
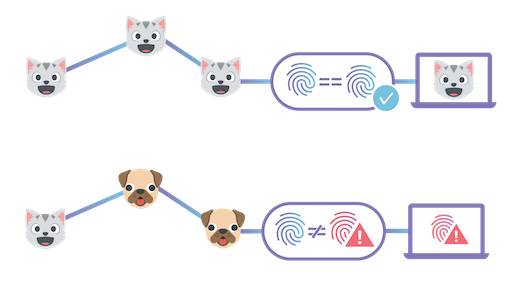
Tampering with content will show up in the IPFS hash. Image: Cloudflare
The Cloudflare gateway allows users to request IPFS-hosted content from a browser (via HTTPS, using a fully qualified file path that includes the content's hash).
For hosting, "you can also build a website that's hosted entirely on IPFS, but still available to your users at a custom domain name. Plus, we'll issue any website connected to our gateway a free SSL certificate, ensuring that each website connected to Cloudflare's gateway is secure from snooping and manipulation."
The company's demonstrations also include an IPFS-hosted searchable archive of StackExchange; this how-to explains how to host a website on the gateway; and there's a bucket of documentation at the IPFS site here.
IPFS is also being discussed as part of a distributed internet infrastructure project at the Internet Engineering Task Force here. ®
