This article is more than 1 year old
Sealed with an XSS: IT pros urge Lloyds Group to avoid web cross talk
Online login details could be harvested by miscreants – bank says: We're secure
A pair of IT workers have criticised banks within the Lloyds Banking Group (LBG) for substandard security. The group denies anything is amiss, maintaining it follows industry best practice on cyber-security.
Each of the three LBG banks – Lloyds, Halifax, and Bank of Scotland – has implemented transport layer security by running https so that transactions run to a secure server. But the three financial institutions are nonetheless vulnerable to a common class of web security vulnerability often exploited by phishing fraudsters: cross-site scripting (XSS) flaws.
A software developer and an infosec researcher have separately said that websites maintained by Lloyds, Halifax, and Bank of Scotland all have an XSS vuln, allowing attackers to potentially read and modify the contents of the login form, as well as subsequent pages such as account information in secure banking sessions.
The issue at the three Lloyds Banking Group subsidiaries were uncovered by software developer Jim Ley and reported to each bank. A lack of response prompted him to approach The Register.
Ley developed a live proof-of-concept, seen by The Reg, for each bank showing how the unresolved web flaws could be leveraged to run login-harvesting phishing attacks.
This illustrates the risk that, unless the flaw is resolved, convincing phishing scams that leverage the web security shortcoming might be developed, he warned.
Independent security researcher Paul Moore confirmed our tipster's warning, adding that Halifax Bank is vulnerable to a somewhat related problem.
"[Halifax Bank's] lack of adequate security headers allows the injection of malicious scripts to both collect and alter anything the user enters, regardless of TLS," Moore told El Reg.
"Banks should deploy the correct security headers before third party dependencies go rogue… many sites are vulnerable if they don't deploy security headers correctly,” he added.
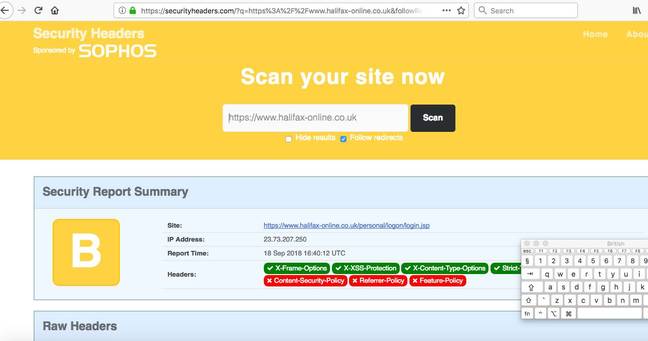
Halifax Bank rates a "B" on Scot Helme's Security Headers benchmark, which may on the surface seem like a passing grade but belies the problem. The devil lies in the detail, according to Moore.
“A ‘B’ isn't bad, but the difference between an ‘A’ and ‘B’ here is the existence of a CSP [Content Security Policy]1 header. If they disallowed inline scripts, they'd get an ‘A’ and wouldn't be vulnerable to this attack,” Moore said.
Moore's (benign) proof-of-concept demo from Halifax Bank can be found here, which he flagged up to the infosec community through Twitter.
El Reg relayed these criticisms to reps at LBG, alongside a request for comment. The bank said it welcomed the reports while downplaying their significance:
We employ multi-layered security controls across our systems. We take responsible disclosures seriously and always follow up to ensure that the best methods are followed.
Both techies were unimpressed with this reply. Each independently stated they had found it difficult to report problems to LBG. "If they made the reporting process easier, I'd be happier," Moore commented.
The Reg has seen an email from LBG’s digital security team to Moore stating they were “aware of this issue”, adding that its techies “are already working on it”. ®
Bootnote
1Content Security Policy is a security technology designed in large part to minimise XSS problems.