This article is more than 1 year old
Google Play Store spews malware onto 9 million 'Droids
How did these get through the net?
Malware made it past Google's detection systems and infected some 9 million Android users, analyst Trend Micro has found. Google has removed 85 apps from the Google Play Store as a result.
The apps, purportedly TV and video players and controllers, would consistently show full-screen ads until they crashed. Developers behind such apps then racked up ad impressions from which they profited.
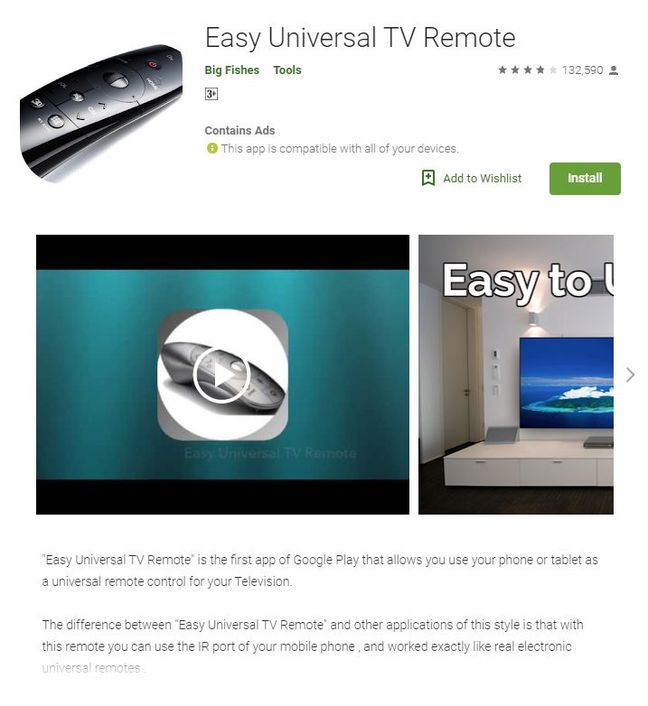
The batch of 85 apps removed included the "Easy Universal TV Remote", which had a high proportion of negative reviews but had managed to evade Google's security filters, Trend Micro noted.
Take, for example, the app below. At a glance it looks harmless enough...
... but did the comments and ratings not raise a flag?
Google claimed to have halved the quantity of Android malware in its first Android Ecosystem Security Transparency Report published in November. But the scale of the ecosystem still means trouble for many. By Google's calculations, only 0.09 per cent of devices accessing the Store had malware on board – but that's still 1.8 million phones.
This batch of apps was hard for the user to miss – some adware continues to generate bogus impressions in the background.
You can find a full list here (PDF). ®