This article is more than 1 year old
'It's like they took a rug and covered it up': Flight booking web app used by scores of airlines still vuln to attack – claim
Security hole can still be exploited to tamper with journeys, warn infosec bods
Exclusive A security hole in a widely used airline reservation system remains open to exploit, allowing miscreants to edit strangers' travel details online, The Register has learned. A fix to close the vulnerability was incomplete, and thus ineffective, it is claimed.
White hats at Safety Detective told us today the security flaw in Amadeus, the web-based reservation system used by nearly half of the world's airlines, was only superficially patched after the glaring hole was privately reported by the team.
The vulnerability revolves around the way Amadeus and airlines identify travelers: each person is assigned a unique booking reference, which is a six-digit alphanumeric string that retrieves their passenger name record (PNR). This record has all their personal details and their journeys. The system is used to manage passengers and flights, and allow government security agencies check the identity of travelers for known baddies.
Bug-hunter Noam Rotem found an Amadeus web script, hosted by individual airlines, that accepts a booking reference in the URL, and if that reference is valid, it returns a page with the passenger's name on it. Armed with a working reference and corresponding name, it's possible to log into the airline's online portal as that stranger, and access and edit the traveler's reservation page and PNR details. That means miscreants can change passenger seat assignments, redirect frequent flyer points to another account, alter or view contact details, or even move or cancel flights.
Due to a lack of brute-force protection, bots could repeatedly hit the vulnerable page, running through as many booking references as possible, and making a note of those that cough up a person's name. The reference and name combinations can then be used to access the reservation page, as described above.
Though Safety Detective reported the issue to Amadeus, and early media reports suggested the bug had been squashed, the infosec biz believes those claims were premature, and that the supposed fix for the flaw was only superficial.
Lipstick on a pig
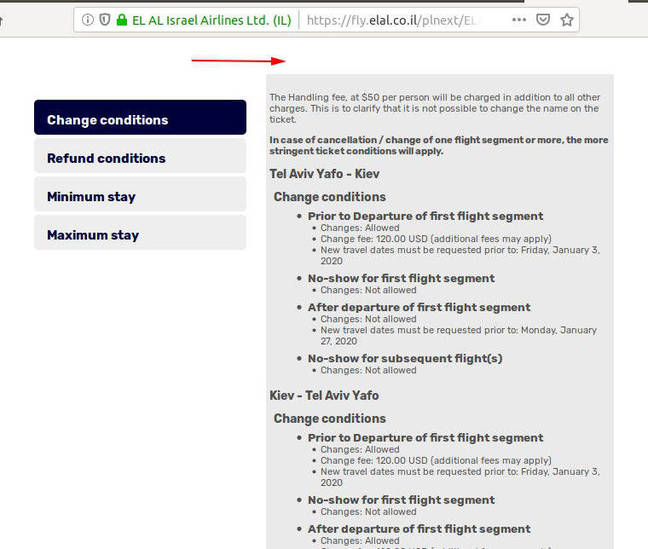
Take for instance, the Israeli airline ELAL, which, like British Airways, Air France, and United Airlines, uses Amadeus for managing its reservations. Safety Detective bods noticed that while the vulnerable flight reservation page was patched to no longer visibly show a passenger's name for a given booking reference...
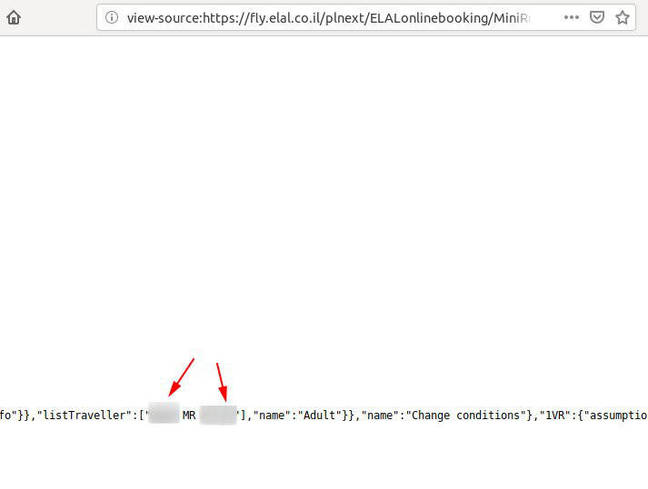
...the HTML source code still contains the person's name in some embedded JSON, it is claimed:
Thus, according to the security biz, you can still supply a reference and get a potential name out of it, which can together be plugged into the airline's online portal to carry out further mischief. There are still no brute-force protections in place, either, we're told.
It seems ELAL is not alone, either. Safety Detective reckons the issue will still be present in all 144 airlines that use the system.
"It is like we told them 'hey there is dirt on the floor, it's not clean,' and they took a rug and covered it up, and said, 'now you don't see it anymore'," Security Detective spokesperson John Brown told us. "Well, we can take the rug off (Ctrl+U in Chrome shows you the code) and see the issue didn't go away just because you (very clumsily) hid it.
"In the brute-force attack, we guess a PNR code, get the flight details, and are then able to change them. Since there is no limitation to the number of attempts, we can guess a good number of valid flights. It's all a matter of time, really. In the screenshot, we show they didn't really fix it. They hid the information in the page, for example, the passenger's name."
Amadeus is urged to curb bot access with CAPTCHAs and limiting the rate of lookups, and introduce some kind of authentication system, such as passwords or passphrases, rather than simply hiding passenger names.
Fiddling while Rome burns
ELAL has been alerted to the purported weak fix. Meanwhile, Amadeus said it is investigating the matter.
"At Amadeus, we give security the highest priority and are constantly monitoring and updating all of our products and systems," a spokesperson insisted to The Register.
"We became alerted to an issue in one of our products and our technical teams took immediate action. We are working closely with our customers and we regret any disruption this situation may have caused.
"We work together with our customers and partners in the industry to address PNR security overall. The airline industry relies on IATA standards that were introduced to improve efficiency and customer service on a global scale.
"Because the industry works on common industry standards, including the PNR, further improvements should include reviewing and changing some of the industry standards themselves, which will require industry collaboration. We are conducting a thorough internal review and detailed investigation into the root cause and impact of this issue and will be working hand in hand with those customers affected."
While researchers have been sounding the alarm on the security of booking references and PNRs, the industry seem reluctant to act. So, too, are regulators, with the EU fumbling a chance to shore up the system. ®