This article is more than 1 year old
Secret mic in Nest gear wasn't supposed to be a secret, says Google, we just forgot to tell anyone
Whoops! Oh gosh
+Comment Google has apologised for not telling Nest smart home kit owners there was a microphone in their gear.
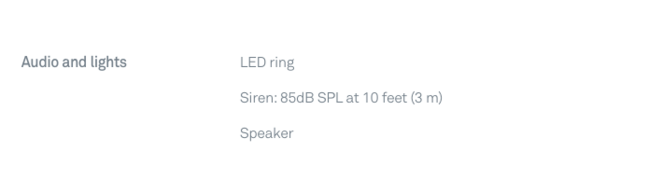
The £99 Nest home alarm talks to Google's servers over the internet, offering home monitoring and alert functions. Here's a snapshot of the product page for the system, taken on 15 December:
And here's how it is today.
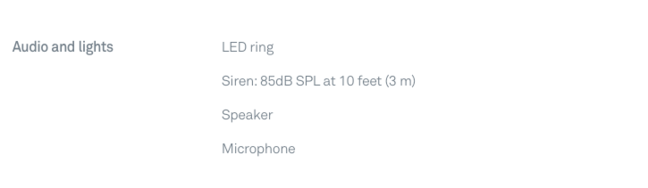
Notice anything different?
The secret mic only emerged when Google told owners it was activating the feature.
"The on-device microphone was never intended to be a secret and should have been listed in the tech specs. That was an error on our part," the company told Business Insider. "The microphone has never been on and is only activated when users specifically enable the option."
Mistakes will happen. A decade ago, Google "mistakenly" put Wi-Fi sniffing into its Google Street View cars, which slurped data from people's home networks as the cars drove past. The "accident" had been patented earlier.
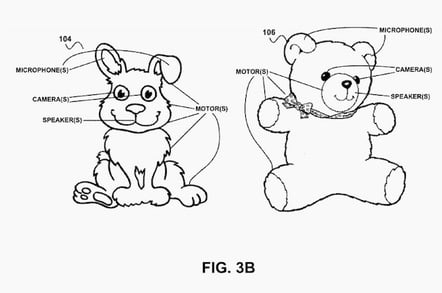
More creepy ideas from the bowels of Google (this is from a patent published in 2015)
Installing a microphone in a burglar alarm makes far more sense than other Google data acquisitions. Google never deletes the wave file of your voice, input via Google Assistant, so the company could (theoretically) match the voice profile of the burglar to one it has stored on file. Useful, no? And a step closer to the pervasive authoritarian surveillance society outlined in The Circle, where author Dave Eggers describes a benevolent big brother, one who really cares for you (there was also a movie).
+Comment
"Surveillance capitalism" (a clumsy phrase) companies bet on convenience trumping privacy concerns as consumers welcome the devices into their homes. But surely these short-sighted users bear just as much responsibility for the trend as the "evil corporation" making them? Complaining about surveillance after acquiring an Alexa or a Google Home is rather like adopting a pet crocodile and complaining when it grows up and devours the children.
Why do you think these companies made them? ®
