This article is more than 1 year old
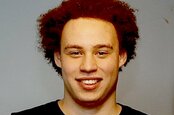
Wannacry-slayer Marcus Hutchins pleads guilty to two counts of banking malware creation
'I regret these actions and accept full responsibility for my mistakes'
Marcus Hutchins, the British security researcher who shot to fame after successfully halting the Wannacry ransomware epidemic, has pleaded guilty to crafting online bank-account-raiding malware.
For nearly two years now, Hutchins, 24, has been living in the US, while out on bail awaiting trial, after being collared in 2017 at Las Vegas airport by FBI agents acting on a tip-off.
The Brit, who was at the time trying to fly back home to Blighty after attending the Black Hat and DEF CON security conferences, was accused by the g-men of creating and selling the Kronos banking trojan, and denied any wrongdoing.
The US government subsequently piled on more criminal charges, and it now appears that the pressure has been too much: on Friday this week, Hutchins accepted a plea deal [PDF], and admitted two charges of malware development.
"I’ve pleaded guilty to two charges related to writing malware in the years prior to my career in security," he said in a statement.
"I regret these actions and accept full responsibility for my mistakes. Having grown up, I’ve since been using the same skills that I misused several years ago for constructive purposes. I will continue to devote my time to keeping people safe from malware attacks."
Each of the two counts carries a maximum penalty of five years behind bars, a $250,000 fine, and a year of probation. As with most plea deals, he's likely to get less than that, though he may still spend some time in an American cooler.
While being held in jail after his arrest, Hutchins apparently admitted creating the software nasty. According to the Feds, the Brit at one point told an unnamed associate over a recorded telephone line: "I used to write malware, they picked me up on some old shit," later adding: "I wrote code for a guy a while back who then incorporated it into a banking malware."
Now the FBI have their guilty plea, and Hutchins – a professional malware reverse-engineer these days – is facing an uncertain future. But you have to wonder if it was all really worth it for the US authorities.
After all, plenty of today's cyber-security engineers and researchers have toyed with writing malware, even for research purposes. Thus, a stretch behind bars would be a very hard sentence for an offense committed when he was a teen. ®