This article is more than 1 year old
The NetCAT is out of the bag: Intel chipset exploited to sniff SSH passwords as they're typed over the network
Cunning data-snooping side-channel technique is tough to exploit, Chipzilla warns
Video It is possible to discern someone's SSH password as they type it into a terminal over the network by exploiting an interesting side-channel vulnerability in Intel's networking technology, say infosec gurus.
In short, a well-positioned eavesdropper can connect to a server powered by one of Intel's vulnerable chipsets, and potentially observe the timing of packets of data – such as keypresses in an interactive terminal session – sent separately by a victim that is connected to the same server.
These timings can leak the specific keys pressed by the victim due to the fact people move their fingers over their keyboards in a particular pattern, with noticeable pauses between each button push that vary by character. These pauses can be analyzed to reveal, in real time, those specific keypresses sent over the network, including passwords and other secrets, we're told.
The eavesdropper can pull off this surveillance by repeatedly sending a string of network packets to the server and directly filling one of the processor's memory caches. As the victim sends in their packets, the snooper's data is pushed out of the cache by this incoming traffic. As the eavesdropper quickly refills the cache, it can sense whether its data was still present or evicted from the cache, leaking the fact its victim had sent over some data. This ultimately can be used to determine the interval between the victim's incoming packets, and thus the keys pressed and transmitted by the victim.
This security oversight is non-trivial to exploit, and Intel doesn't think this is a big deal at all, though it is nonetheless a fascinating weakness that you may want to be aware of. Bear in mind, the snooper must be directly connected to a server using Intel's Data Direct I/O (DDIO) technology. Also, to be clear, this is not man-in-the-middle interception nor a cryptography crack: it is a cache-observing side-channel leak. And it may not work reliably on a busy system with lots of inbound interactive data.
How it works
DDIO grants network interfaces the ability to write data directly into the host processor's last-level cache, bypassing the system RAM. In practice, this lowers latency and speeds up the flow of information in and out of the box, and improves performance in applications, from web hosting to financial trading, where I/O could be a bottleneck.
Unfortunately, as boffins at VUSec – the systems and network security group at Vrije Universiteit Amsterdam in the Netherlands – have found, that leap into the CPU cache opens up the potential for side-channel holes. Earlier this year, the white-hat team uncovered and documented the aforementioned method in which a miscreant can abuse DDIO to observe other users on the network, and, after privately disclosing the flaw Intel, went public today with their findings.
DDIO is, for what it's worth, enabled by default in all Intel server-grade Xeon processors since 2012.
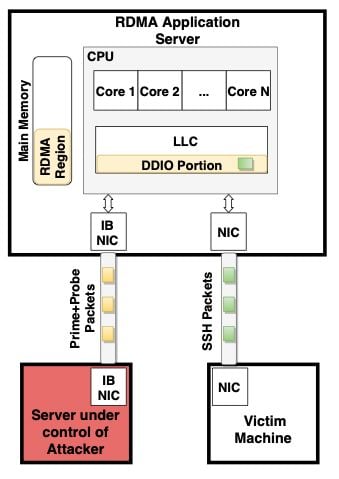
The technique, dubbed NetCAT, is summarized in the illustration below. This particular exploitation approach, similar to Throwhammer, requires the eavesdropper to have compromised a server that has a direct RDMA-based Infiniband network connection to the DDIO-enabled machine in use by the surveillance target. This would require the snooper to have gained a foothold in the organization's infrastructure.
Once connected, the spy repeatedly fills the processor's last-level cache over the network, effectively flooding the cache with its own data. The snoop observes slight variations in the latency of its connection to detect when its data is evicted from the cache to RAM by another network user, a technique known as prime+probe. The timing of these evictions leaks the victim's keypresses.
Crucially, a portion of this last-level cache is reserved for this direct IO use, thus the prime+probe method is not troubled by code and application data running through the CPU cores.
All this means the underlying hardware may inadvertently divulge sensitive or secret information. More technical details on NetCAT are due to be formally published in May next year.
"Cache attacks have been traditionally used to leak sensitive data on a local setting (e.g., from an attacker-controlled virtual machine to a victim virtual machine that share the CPU cache on a cloud platform)," explained the VUSec team, which was awarded a security bug bounty by Intel for its discovery.
"With NetCAT, we show this threat extends to untrusted clients over the network, which can now leak sensitive data such as keystrokes in a SSH session from remote servers with no local access.
"In an interactive SSH session, every time you press a key, network packets are being directly transmitted. As a result, every time a victim you type a character inside an encrypted SSH session on your console, NetCAT can leak the timing of the event by leaking the arrival time of the corresponding network packet."
Armed with the timing of the packets, an attacker could potentially match these intervals to specific keystrokes by comparing observed delays to a model of the target's typing patterns.
The end result, as shown below, is a method for spying on SSH sessions in real time with nothing more than a shared server:
In an FAQ, the academics set out what specifically is at risk:
If DDIO is available/enabled on your platform, you are affected by the vulnerability. If RDMA is also enabled, the vulnerability immediately exposes your server to practical side-channel attacks over the network, as demonstrated by our NetCAT exploit.
And if you were wondering about this name of the design flaw:
We do not believe in fear-mongering with our research. NetCAT stands for Network Cache ATtack. “netcat” is also a famous utility that hackers and system administrators use to send information over the network. cat is the UNIX tool to read the contents a file, netcat is supposed to do the same over the network. NetCAT is a pun on being able to read data from the network without cooperation from the other machine on the network. If that is not enough pun already, DDIO makes use of the Cache Allocation Technology (CAT) internally. Finally, who doesn’t like cats?
If all of this sounds rather complex and unfeasible in real life, well, it is. The scenario VUSec laid out is mostly a proof-of-concept rather than a practical attack scenario, according to Intel, at least.
"Intel received notice of this research and determined it to be low severity (CVSS score of 2.6) primarily due to complexity, user interaction, and the uncommon level of access that would be required in scenarios where DDIO and RDMA are typically used," a Chipzilla spokesperson told The Register.

Deja-wooo-oooh! Intel chips running Windows potentially vulnerable to scary Spectre variant
READ MORE"Additional mitigations include the use of software modules resistant to timing attacks, using constant-time style code. We thank the academic community for their ongoing research."
As with most side-channel leaks, while the process of actually exploiting the bug is potentially tedious and unlikely, it demonstrates a fundamental flaw that can be difficult, if not impossible, to address with anything short of a hardware redesign.
While VUSec agrees with Intel that adding software protections against timing attacks will hamper NetCAT-based spying, the only sure way to remove the vulnerability is to disable DDIO entirely, and lose the performance benefits.
"As long as the network card creates distinct patterns in the cache," the VUSec team said, "NetCAT will be effective regardless of the software running on the remote server." ®