This article is more than 1 year old
Chinese e-commerce site LightInTheBox.com bared 1.3TB of server logs, user data and more
Things you don't do with Elasticsearch dbs, number 1: Put them on the web
Exclusive Infosec researchers have uncovered a data breach affecting 1.3TB of web server log entries held by Chinese e-commerce website LightInTheBox.com.
Noam Rotem and Ran Locar, VPN comparison site VPNmentor’s research team, uncovered the breach in late November.
The data was “unsecured and unencrypted”, accessible from an ordinary web browser and was being held on an Elasticsearch database, which, as the two noted, “is ordinarily not designed for URL use”.
“The database [we found] was a web server log – a history of page requests and user activity on the site dating from 9th of August 2019 to 11th of October,” said the two researchers in a statement about their findings shared with The Register, adding that it appeared to contain around 1.5bn entries.
The server logs included user email addresses, IP addresses, countries of residence and pages each visitor viewed on LightInTheBox’s website. It also contained data from the company’s subsidiary sites including MiniInTheBox.com.
LightInTheBox is a typical online retailer selling retail goods such as gadgets, clothing and small accessories. The site has very few clues about its Chinese origins other than sponsored links at the bottom of its homepage with a distinctly Chinese theme.
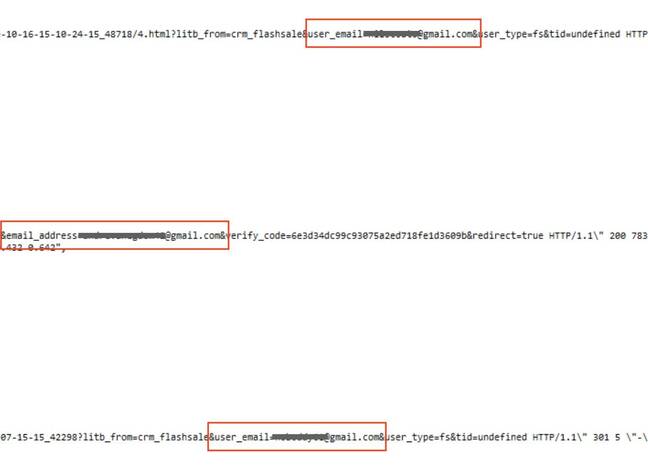
Code snippets shared with The Register showed precisely how users’ email addresses were exposed.
Aside from LightInTheBox.com, the breached database also contained data from the firm’s subsidiary sites, including MiniInTheBox.com. LightInTheBox itself is said to have around 12m monthly visitors to its site.
Opining that the breach is a big problem for LightInTheBox, Rotem and Locar said: “This data breach represents a major lapse in LighIinTheBox’s data security. While this data leak doesn't expose critical user data, some basic security measures were not taken. This is a time of the year with a lot of online shopping: Black Friday, Cyber Monday, Christmas. Even a large leak with no user Personally Identifiable Information data could be a threat to both the company and its customers.”
With access to users’ email addresses and precise browsing history, a malicious group could easily craft targeted phishing emails pretending to be, for example, followup messages from LightInTheBox itself offering discounts on previously-viewed products.
Buried in LightInTheBox’s online privacy policy is the line: “While our business is designed with safeguarding your personal information in mind, please remember that 100% security does not presently exist anywhere, online or offline.”
Too true. Full details of vpnMentor's findings will be on their website.
Although LightInTheBox did not respond to Rotem and Locar’s enquiries, the breach was closed off shortly after the New York Stock Exchange-listed Chinese company was told about it. El Reg was unable to find a method of contacting LITB other than by registering a customer account and opening a support ticket. ®