This article is more than 1 year old
This page is currency unavailable... Travelex scrubs UK homepage, kills services, knackers other sites amid 'software virus' infection
Systems still toast since NYE compromise, manual processing only
Foreign currency mega-exchange Travelex said on Thursday it was forced offline by a "software virus" infection, bring down a number of currency-exchange websites with it.
In a statement shared on Thursday, the UK-headquartered biz said the digital nasty, first spotted on New Year's Eve, caused it to unplug its UK site and online services while it worked to clear up the mess.
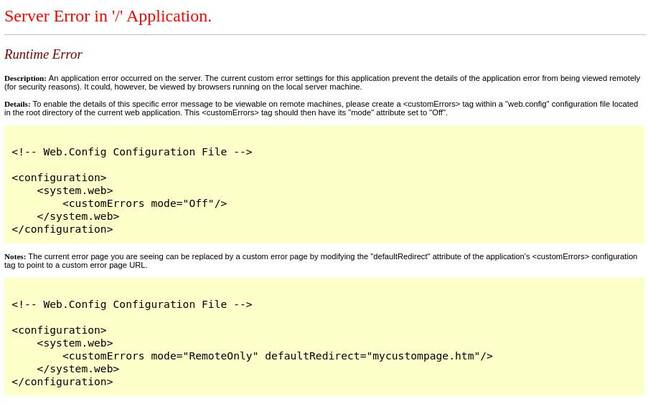
In-person transactions at bureaus and airports are still continuing albeit using manual processing, and we're told customer data has not been accessed by miscreants. At the time of writing, travelex.co.uk was still offline and showing a runtime error message.
"As a precautionary measure in order to protect data and prevent the spread of the virus, we immediately took all our systems offline," the statement reads. "Our investigation to date shows no indication that any personal or customer data has been compromised."
The outage at Travelex has had a knock-in effect in that it knackered currency-swap services for a number of UK banks and organizations relying on the exchange. These include Tesco, HSBC, and Virgin Money, with Barclays, Sainsbury's, and First Direct also said to be affected.
Travelex could not say when it expected the services to be back online. The biz said it has "teams of IT specialists and external cyber security experts," working on the issue, but there's no reported progress so far.
While no details were given on just what the infection was or how it got onto the network, Brit infosec watcher Kevin Beaumont pointed out Travelex had public-facing Windows remote-desktop servers with no Network Level Authentication enabled – that's the feature that requires users to authenticate before they can establish a session and attempt to login.
Travelex’s AWS platform had Windows servers with RDP enabled to internet and NLA disabled, oops. pic.twitter.com/UJz7pQJwx6
— Kevin Beaumont (@GossiTheDog) January 2, 2020
One hopes Travelex has patched these systems for BlueKeep and other security holes.
As some of you have spotted, Travelex is using Windows Server 2008 R2 with .NET 4.0.30319, which is rather out of date. ®