This article is more than 1 year old
Lettuce Encrypt, Encrypt We Must: Hobby projects change name after Let's Encrypt fires off trademark complaints
One's 'best served cold with ranch and carrots', the other turns to 'Yoda Speak'
Updated An open-source project for automating the installation of free Let's Encrypt certificates for websites built with Microsoft's ASP.NET Core framework was forced to change its name after a trademark complaint from the Internet Security Research Group (ISRG).
ISRG is nonprofit sponsored by numerous companies including the Electronic Frontier Foundation, Google, Cisco, Mozilla, Facebook, IBM, VMware, Akamai, and Microsoft-owned GitHub. Its purpose is to promote secure internet connections, its main project being Let's Encrypt. Using the Let's Encrypt service, anyone can obtain a free SSL certificate so that it costs nothing to support encrypted connections on a website. Let's Encrypt issued its first certificate in 2015.
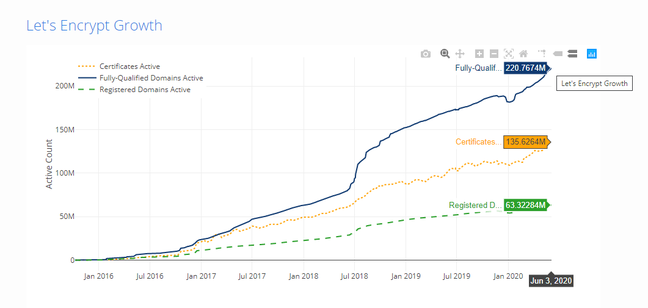
Let's Encrypt has been hugely popular, and has now certified over 220 million active domains, according to its statistics, but has some inconveniences, notably that its certificates expire after 90 days. The idea is to reduce the risk from compromised certificates, and to encourage automated renewal.
The primary tool for obtaining a Let's Encrypt certificate is a script called certbot, but for a long time this did not work on Windows. Although there is now a Windows version, it has limitations like the inability to update the webserver automatically. It was designed with Unix-like operating systems in mind and has always been a tad awkward for Windows users. The availability of other scripts has improved since the early days; many are listed here, some specifically for Windows.
Nate McMaster worked at Microsoft when Let's Encrypt was launched (he is now a software development engineer at AWS) and started a "hobby project" to provide a Let's Encrypt API for ASP.NET core applications. "When enabled, your web server will automatically generate an HTTPS certificate during startup," explain the docs. "It then configures Kestrel to use this certificate for all HTTPS traffic." Kestrel is the default ASP.NET web server. He called the project ASP.NET Core + Let's Encrypt. McMaster's solution does not actually auto-renew certificates according to a schedule, though this is a possible forthcoming feature.
It seems that ISRG considered that the project did not conform to its trademark policy. "Earlier versions of this package were named 'McMaster.AspNetCore.LetsEncrypt', a name selected from combining my family name, the web framework for .NET Core, and the most widely used certificate authority that implements the ACME protocol, which is 'Let's Encrypt®', of course," McMaster explained on the project's GitHub issues page.
"This was started as a hobby project years ago and I never thought the naming would be a problem. This project drew the attention of the Internet Security Research Group (ISRG)™️, which runs Let's Encrypt. They informed me last week that they considered my original project name a violation of their trademarks. As this code is not an official offering of ISRG and I want to support their efforts to run Let's Encrypt, I have complied with their request to rename the project."
The name he chose is Lettuce Encrypt – "100% organic and best served cold with ranch and carrots."
It is unfortunately a breaking change but should require "minimal effort" to upgrade. The old version is still available from nuget.org, the .NET package repository, but is now unsupported. In December, McMaster considered abandoning the project because of similar competing solutions, but following feedback decided to "keep working on this project" and invited feature suggestions.
The main similar project McMaster had in mind is called "AspNet.EncryptWeMust" (which does auto-renew) and guess what? "This project used to be called FluffySpoon.AspNet.LetsEncrypt, but due to a trademark claim from LetsEncrypt, we had to rename it. The name now follows Yoda Speak," says maintainer Mathias Lykkegaard Lorenzen.
Whether Lettuce Encrypt is useful depends on the exact hosting scenario. It only works for Kestrel, and not when the application is behind IIS, the Windows web server (though note that ASP.NET Core is cross-platform and also runs well on Linux). It does not work with Azure App Service (though the Yoda-Speak alternative does), perhaps the most common way to deploy an ASP.NET Core application to Microsoft's cloud.
There are other options, such as Simon Pedersen's Let's Encrypt Site Extension. In addition, paying Azure customers can get free SSL certificates from DigiCert via Microsoft's App Service Managed Certificates, now in preview. A limitation of Microsoft's official service is that it does not support naked domains; developers must use a prefix such as www.
Heavy-handed or just going through the motions needed to protect its trademark? We have asked ISRG for comment. ®
Updated at 08:55 UTC on 11 June to add
ISRG got back to us and gave three reasons for its actions. First, "If we were to let independent third parties use our name and brand, then our reputation would depend on their actions, over which we have no control," the company said.
Second, "If third party software offerings use our Let's Encrypt brand name, they have the potential to confuse users, who will not be sure if any given 'Let's Encrypt' software package originates from us or from a third party, like the projects in question here."
Third, "If we do not enforce our trademark rights, we run the risk of losing them."
What then should you do if you create utilities that interact with Let's Encrypt - since the point of the service is to encourage admins to automate certificate renewal and the official script does not cover all scenarios?
"Client software that works with the Let's Encrypt service must implement the ACME certificate management protocol, something we developed and helped to standardize," said ISRG. "We made it an open protocol so that any CA can use it, and client software can work with multiple CAs using the same protocol. We recommend that client software compatible with Let's Encrypt use the term ACME in its name, because it more accurately describes what the software does while not implying its use is limited to just our service."