This article is more than 1 year old
North Korean hackers pwned cryptocurrency sysadmin with GDPR-themed LinkedIn lure, says F-Secure
Click here to enable your rights... ha, GOTCHA!
Infosec biz F-Secure has uncovered a North Korean phishing campaign that targeted a sysadmin with a fake Linkedin job advert using a General Data Protection Regulation (GDPR) themed lure.
The sysadmin worked for a cryptocurrency business, said the threat intel firm, which made him a ripe target for the money-hungry state hackers Lazarus Group, aka APT38, supposedly backed by North Korea.
"Our research, which included insights from our incident response, managed detection and response, and tactical defence units, found that this attack bears a number of similarities with known Lazarus Group activity, so we're confident they were behind the incident," said F-Secure's director of detection and response, Matt Lawrence.
North Korean attackers targeted "organizations in the cryptocurrency vertical" based in Britain, the US, the Netherlands, Germany, Singapore, Japan, and at least eight other countries, said F-Secure.
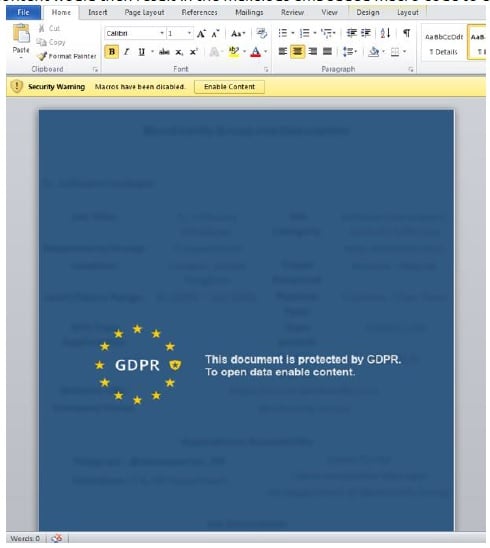
The initial lure was a malware-infected file sent as an attachment to a LinkedIn message, urging the sysadmin recipient to open it for details of an exciting new job. Once opened, the file displayed this:
"As can be seen in the [above] image, the malicious version of the document claimed to be protected by General Data Protection Regulation (GDPR) and that content needed to be enabled in Word to access the document. The enablement of content would then result in the malicious embedded macro code to execute," said F-Secure.
Malicious files downloaded after the macro was run bore similarities to previous APT38 tools uncovered by Russia's Kaspersky Lab in 2016.
"Lazarus Group invested significant effort to evade the target organization's defences during the attack, such as by disabling anti-virus software on the compromised hosts, and removing evidence of their malicious implants. And while the report describes the attack as sophisticated, it points out Lazarus Group's efforts to hide their presence were not enough to prevent F-Secure's investigation from recovering evidence of their activities," said F-Secure in a canned statement.
Lazarus Group is well known for targeting financial institutions in order to siphon money back to North Korea, whose economy has stagnated for decades under Western-led sanctions intended to persuade the Communist dictatorship not to develop nuclear weapons.
In 2014 the state-backed hackers targeted Sony Pictures, stealing sensitive internal files; in 2016 they stole $81m from a Bangladeshi bank; a year later it was revealed they were targeting everything from casinos to software devs working on financial software; and last year they went completely beyond the pale by deploying in-memory malware for macOS. The group is also thought to have been behind the Wannacry malware that temporarily crippled Britain's National Health Service.
The crew is well known for using social engineering lures to deploy its malware, as well as for leaving such obvious clues to their identity that infosec researchers regularly wonder if they're seeing a false flag attack. ®