This article is more than 1 year old
Microsoft promises end-to-end encrypted Teams calls for some, invites you to go passwordless with Azure AD
When there are passphrases, there is inherent risk, says Redmond
Ignite Microsoft has said it will add end-to-end encryption for some one-to-one Teams calls later this year – and urged folks to move away from using passwords with Azure AD.
The Teams improvements, announced at the tech giant’s Ignite conference this week, will be available "to commercial customers in preview in the first half of this year."
"In this first release, customers will have the ability to enable E2EE for 1:1 unscheduled Teams calls," Redmond said. "Customers will be able to specify which members of their organization can use E2EE. Future updates will be made available to support customers’ evolving compliance needs, including expanding to scheduled calls and online meetings."
Among the large array of collaboration software, almost all of which had seen a massive increase in use thanks to the global pandemic, most services don’t provide a proper end-to-end encryption solution, instead relying on encryption of data in transit – typically TLS – and different encryption when stored on servers.
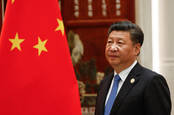
Microsoft fixes four zero-day flaws in Exchange Server exploited by China's ‘Hafnium’ spies to steal victims' data
READ MOREThat provides a goodish level of security but doesn’t ensure that communication is only visible and understandable to the people actually talking to one another. Video conferencing rival Zoom offers end-to-end encryption with a few caveats and additional steps, and that appears to be more or less the approach Microsoft will take, too.
Microsoft also said passwordless authentication in Azure Active Directory is now generally available. Thus, Azure AD users can ditch typed-in passwords altogether, and instead use things like biometrics (facial recognition and fingerprints) or separate authentication apps or hardware keys to log into accounts.
No matter how many times it is drilled into people that using non-complex passwords or reusing passwords is a security risk, people still do it, making life easier for miscreants to break into accounts. While it's relatively easy to phish someone's passphrase, it's more tricky – though not impossible – to do so if the target uses multi-factor authentication.
“When there’s passwords there is inherent risk to the organization,” Microsoft’s VP of security, compliance, and identity marketing Vasu Jakkal told Yahoo! “It's a long journey but we do hope that passwordless is going to be a norm. It is a safer way to do things and so the more we can all embrace that I think the more we can protect ourselves and our organizations.”
- Microsoft touts Azure Percept development kits to those toying with AI on the edge
- Excel-lent: Microsoft debuts low-code Power Fx language... but it is not really new
- Microsoft previews Windows Server 2022: Someone took a spanner to core plumbing features
Microsoft supports a bunch of passwordless authentication solutions, such as its own Windows Hello facial recognition, fingerprint readers similar to many modern mobile phones, its Microsoft Authenticator app that provides a time-limited login authorization code, and physical things like USB fobs that use the FIDO security standard.
It also talked up something called Temporary Access Pass, which will provide an Authenticator-style time-limited short code that sysadmins can send people for initial logins or for recovering access.
You can find a load of other security-related announcements here.
This all follows the news of the mass hacking of government departments and Fortune 500 companies by suspected Russian-government hackers who backdoored SolarWinds' network monitoring software. Some of Microsoft's own source code was swiped by the cyber-spies during this espionage campaign. ®
PS: Microsoft also made its enterprise-grade Power Automate Desktop tool free for Windows 10 users.
