This article is more than 1 year old
iFixit publishes teardown of M1 iMac, shows that making a determination of repairability is still hard
No alarms, no surprises
We’ve crossed the point where teardowns of Apple’s computers cease to be a genuine assessment of fixability, and become an intellectual exercise into seeing how they’re built. iFixit’s preliminary teardown of the 24-inch M1 iMac is a good example of this.
As expected, it’s just as unservicable as all the other M1 Macs, with soldered storage (in this case, a 128GB Kioxia NAND module) and RAM located on the processor package (namely two SK Hynix LPDDR4x modules).
Whereas the previous Intel iMacs allowed some degree of upgradability, the Apple Silicon variant ultimately does not. No surprises here. These are where the winds have shifted industry-wide.
At least disassembly is familiar, albeit not exactly straightforward. As was the case with previous iMacs, the avenue of ingress was through the screen.
Apple affixed the display directly to the protective glass cover, allowing iFixit to detatch the pair with one swift movement. With little adhesive used, it cut through the glue with a miniature pizza wheel without having to apply any heat first.
By contrast, Apple previously treated both components as discrete units, with some models notorious for the amounts of rock-hard adhesive used. Admittedly, this approach had its own advantages. If you damaged the glass, that was all you had to replace. On the flip side, it also made it easier to damage the delicate LCD panel lurking underneath.
From this, we can infer that the latest 24-inch iMac allows for easy display replacements. But The Reg wouldn't be too certain.
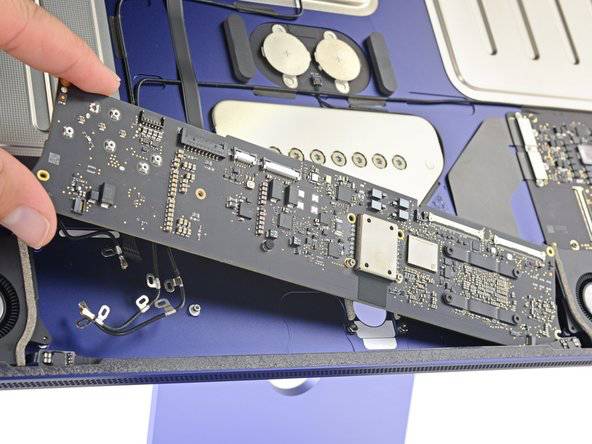
The fanless M1 MacBook Air-sized logic board is housed in the artificial "chin" of the iMac (click to enlarge). Pic courtesy iFixit
In recent years, Apple has shown an unsettling enthusiasm for component serialisation. This effectively means individual components are linked to the logic board, preventing third-party repair shops from using donor parts obtained from other faulty devices. The iPhone 12 is the best example of this.
If you switch a camera from one iPhone 12 to another, it won't work properly. If you re-use a display panel, Apple will disable TrueTone and warn the owner they're using a non-genuine part, as recently noted by Aussie right-to-repair advocate Hugh Jeffreys.
- Big right-to-repair win: FTC blasts tech giants for making it so difficult to mend devices
- Apple, forced to rate product repair potential in France, gives itself modest marks
- Calls for 'right to repair' electronics laws grow louder across Europe
- Cool, cool, cool: Screwdriver-wielders delve into the guts of an Xbox Series X
Until software workarounds are discovered, the only way around this is to seek repairs from the Genius Bar, or another Apple-certified technician.
And so, it's really hard to make a determination as to whether the inaugural Apple Silicon enjoys a modicum of repairability from a simple teardown alone.
iFixit is expected to continue with its teardown later today, with the sound system and Magic Keyboard due an investigation. The right-to-repair group will also issue a repairability score. ®

