This article is more than 1 year old
UK and chums call out Chinese Ministry of State Security for Hafnium Microsoft Exchange Server attacks
And US indicts four Chinese spies on suspicion of the hacks
The Microsoft Exchange Server attacks earlier this year were "systemic cyber sabotage" carried out by Chinese state hacking crews including private contractors working for a spy agency, the British government has said.
Foreign Secretary Dominic Raab said this morning in a statement: "The cyber attack on Microsoft Exchange Server by Chinese state-backed groups was a reckless but familiar pattern of behaviour. The Chinese Government must end this systematic cyber sabotage and can expect to be held to account if it does not."
Through using four zero-day vulns in Exchange Server, the attackers were able to conduct an espionage campaign against western governments, defence and aerospace firms, education institutions and more. Immediate patches were issued within a week, with long-term fixes deployed as part of April's Patch Tuesday run.
Raab's condemnation of China was echoed by the EU, which said its member states "strongly denounce these malicious cyber activities, which are undertaken in contradiction with the norms of responsible state behaviour as endorsed by all UN Member States."
NATO also expressed "solidarity" with victims of the Exchange Server hacks, saying it was "determined to employ the full range of capabilities, as applicable, at all times to actively deter, defend against, and counter the full spectrum of cyber threats."
Meanwhile, the US Department of Justice charged four Chinese men [PDF, 28MB] with operating a front company in Hainan Province, southern China, for carrying out the Exchange Server attacks.
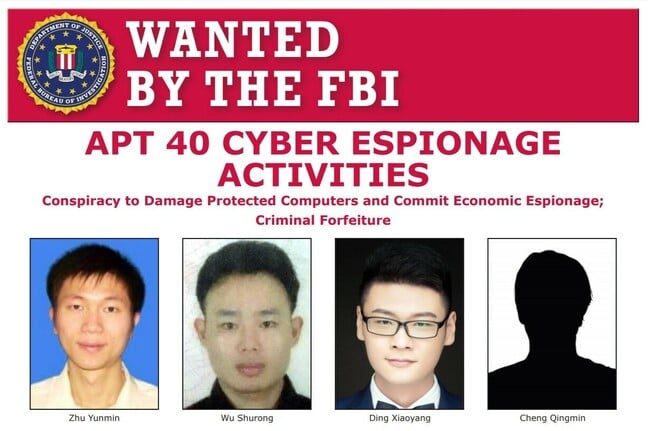
FBI wanted poster for alleged members of APT40, aka China's Ministry of State Security hackers
Today's attribution by the National Cyber Security Centre mirrors four-month-old findings from Microsoft, though the NCSC's version goes into greater detail. When the Exchange Server campaign came to light in March, Microsoft attributed the zero-day exploitations to "a state-sponsored threat actor" that was "based in China."
The attributions are therefore not new but do represent the first formal acknowledgment by western governments that the two APTs behind Hafnium operated with the approval of the Chinese government in Beijing.
The Exchange Server zero-days were also used to spread ransomware, and it is not clear from today's announcements whether the UK and US are explicitly blaming China's government for that as well. Rumours were going around that a behind-closed-doors warning by Microsoft to security partners in late February was leaked, allowing criminals to abuse the zero-days just as patches were published.
Lifting the lid on Hafnium
Although Microsoft's security staff nicknamed the Exchange Server attackers Hafnium, they are publicly tracked as APT31 and APT40.
"NCSC judge that APT40 is highly likely to be sponsored by the regional MSS security office, the MSS Hainan State Security Department (HSSD)," said the British infosec agency today.
The MSS was seen targeting "naval defence contractors across the US and Europe" as well as "regional opponents of the Belt and Road initiative," China's multinational infrastructure construction initiative that has been criticised for leaving partner countries with hefty loans to pay off. Some academics dispute this interpretation of the Belt and Road Initiative as a "debt trap", though the intent is clearly to establish Chinese dominance of new roads and rail links across the world.
Back in 2019, FireEye published research into a five-year espionage campaign by APT40 directed at naval and maritime companies, stealing intellectual property in order to boost China's warship design and construction efforts.
APT 31, meanwhile, is thought to be a "group of contractors" working for the MSS since last year. Its operators target governments, political parties and "service providers", and were responsible for targeting the Finnish parliament in late 2020.
NCSC ops director Paul Chichester said in a statement: "It is vital that all organisations continue to promptly apply security updates and report any suspected compromises to the NCSC via our website." ®
