This article is more than 1 year old
Snyk: 50% of security jobs unfilled… any solution predicated on devs 'becoming security experts is doomed'
Guy Podjarny on the challenges of crafting and shipping secure code
Interview In an interview with Snyk founder and president Guy Podjarny on the challenges of secure application development, he told us: "Any solution that predicates on developers becoming security experts is doomed to fail."
Snyk began in July 2015. Why the name? "The original idea that I had was around sneaking information out to a repository that would then give you insights about it and I said I'll spell it with a y like the cool kids do … and I found out when I Googled it that it's short for So Now You Know," he told us.
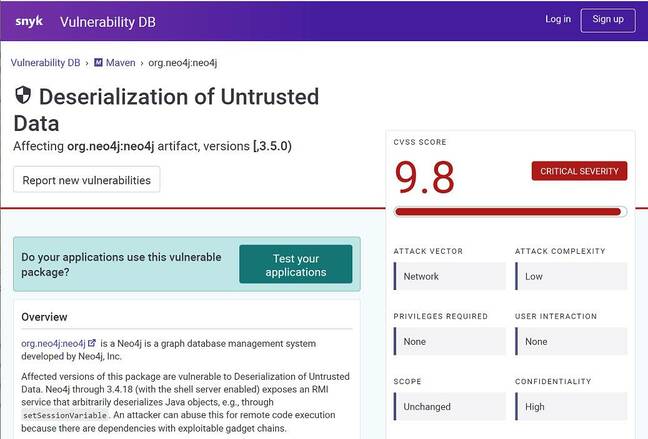
Podjarny's position on developers and secure code isn't terribly surprising: his company provides security tools for programmers. "Snyk's core is the notion of dev-first security. That's our thesis, that's our reason for existence," said Podjarny. Snyk maintains a vulnerability database that records security issues found in open-source software libraries.
"The first problem we tackled has been open source security, and in open source security there's a gap around what vulnerabilities exist. The CVE system is designed for appliances and large enterprises to inform users of flaws, but the community of open source maintainers is not equipped to deal with that," said Podjarny. When vulnerabilities are discovered in an open source project, it gets fixed, noted in release notes, and then it "disappears into the ether of GitHub," he told us.
"We listen to the firehose of information across social, research, open source activities, and we funnel this to our analysts who then curate the vulnerabilities and add the necessary information to it … the job that we do is both the discovery of what's out there and the security expertise to help developers, who are not security experts by and large."
"This type of service is necessary," Podjarny continued. "The open source community is not the best at curation and ongoing maintenance of data assets. Even in operating systems, you see Canonical and Red Hat curating patches and fixes for operating systems. We are doing the same for application dependencies."
Snyk takes a curation approach rather than a crowdsourced approach, said Podjarny. "We believe consumers want our expert opinion on what is a vulnerability and what is not, in collaboration with the maintainer."
There are around 40 people who work on the database, said Podjarny, but it is a combination of manual processing and automation. "Some are building rules on what to inspect, some are building the technology to make those analysts more efficient," he said. "We use our own vulnerability detection software in Snyk Code to help inform us."
Snyk Code
Snyk Code is the company's newest major service, and arose out of the acquisition of DeepCode in October last year. DeepCode specializes in "semantic code analysis powered by AI."
The service has a number of features including scanning code for vulnerabilities whenever a file is saved, or monitoring a Git repository, or as part of a CI/CD process.
One of the problems for developers is picking out which vulnerabilities matter in their specific application, when the amount of data available on possible vulnerabilities can be overwhelming. So Snyk Code is designed to help fix that.
"Security is about risk management," said Podjarny. "It has to start by being aware that a risk exists. It's easy to just not tell you about vulnerabilities, but that is not the best way to make you secure. Once given, the solution comes from a combination of security intelligence, application intelligence, and developer experience."
- How to use Google's new dependency mapping tool to find security flaws buried in your projects
- Google Play puts Android apps on notice: No naughty JavaScript, Python, Lua
- Docker Desktop no longer free for large companies: New 'Business' subscription is here
- Just 2.6% of 2019's 18,000 tracked vulnerabilities were actively exploited in the wild
Contextualizing is key, he told us. "We look to see, does your code call into this vulnerability? We are now building capabilities that assess whether you are configured in a way that your code will be vulnerable. We are working on bringing infrastructure analysis, from our containers and infrastructure as code analysis, to further refine it. We already look at Kubernetes configurations to tell you if a vulnerability is in a system that is publicly accessible," he said.
There is also a focus on making remediation easier, even sometimes generating pull requests with the fixes in them.
"Most developers agree that security is part of code quality. The challenge is that security is naturally invisible, it doesn't have a feedback loop. It doesn't hurt until it hurts very bad. Part of the value of the security solution is to raise that visibility, while not becoming another routine that you learn to get desensitised to," Podjarny said.
You can be secure all the way to bankruptcy
Should developers therefore configure their CI/CD with Snyk Code, or something like it, so that code with detected vulnerabilities cannot be deployed? "Different systems require different levels of security. For some systems like an operating system on which most of the world is operating, the bar is very high. For most applications, that is not the bar," he said.
"Technically it's very feasible to disallow any flaw identified whether high or low severity. In practice it's not the right decision for most businesses. You can be secure all the way to bankruptcy. You also need to be competitive. The trick not to ignore those risks but rather make an intelligent decision about when is a risk worthy of attention and when you can just push forward.
"Snyk's job is to make it easier to develop securely and still stay fast." It should work like a spell-checker in the IDE rather than getting in the way, he explained.
What's different about Snyk Code versus other approaches? "Historically, static analysis tools have tried to understand every path that a program might make," said Podjarny.
"Snyk Code takes more of a data approach, and applies machine learning, so it analyses every file, stores its knowledge, and gets smarter as it processes that data. That makes it dramatically faster than the prior generation, which makes it actually usable," he added.
"Where past generations focused on rules and understanding, Snyk Code benefits from all the code that it can see, including all of the history of all the code at GitHub, to understand how code flows and how it is fixed. This machine learning scales static analysis to the pace of modern software development."
"To date, SAST (Static Analysis Security Testing) is really the poster child of how terrible security tools can be for developers, how poor their signal to noise ratio is. Snyk Code changes that," he claimed. He also highlighted that the tool works on source code rather than needing to be part of the build process, because "that is how developers work."
What can programmers do to shore up their code?
Tools aside, what can developers do to improve the security of their work? "You need to care about it," said Podjarny, "and to embed it into your regular conversations. Whatever security metrics you choose, discuss them in your daily standups, make them part of your core KPIs. It starts with people and with attention given.
"From a practices perspective, you need to start embracing what is the minimum set of data and permissions you need to get, versus the maximum."
In a microservices architecture, "the only way to achieve a secure system is to minimize what each of these parts can do. The natural tendency of developers is to get maximum. Permissions are one of those things that keeps expanding and expanding, until someone adds an asterisk and it ends."
High code velocity is also a factor, Podjarny said. "There's a lot of data already … it shows that speed, if applied correctly, actually improves security. The one caveat is that you have to have speed plus visibility … I personally advocate for continuous pipelines that raise the right awareness but are relatively light in actually breaking the build."
Is Google right in saying that there is a global problem caused by lack of security specialists, for Linux but also elsewhere?
There is an absolute security talent shortage in the world and roughly 50 per cent of security jobs remain unfilled
"There is an absolute security talent shortage in the world and roughly 50 per cent of security jobs remain unfilled," said Podjarny. "Security is a deep expertise and not one that is easy to acquire. And any solution that predicates on developers becoming security experts is doomed to fail.
"Developers have to do everything, they are only human. I believe the problem is real, and the solution is to have security plans that include more leverage, like tools, like more secure platforms that remove certain security concerns. For example the mobile security world has built platforms and operating systems that are inherently more secure than desktop operating systems. Cloud offers an opportunity to rethink security in the same fashion."
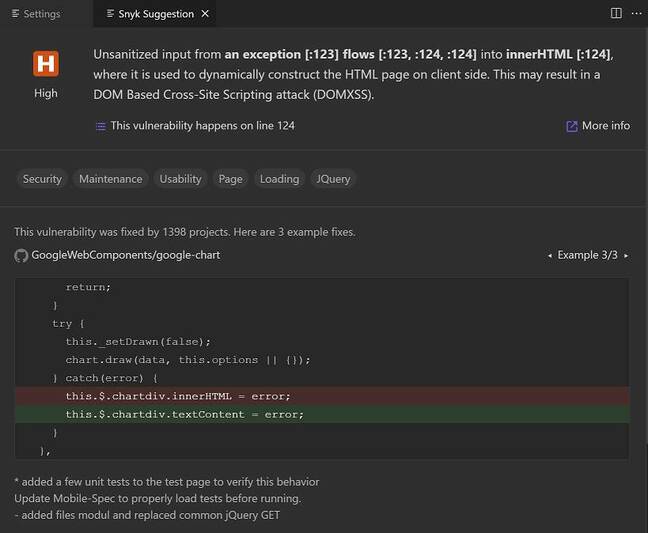
We took a quick look at Snyk Code, via a Visual Studio Code extension. Note that it uploads code to Snyk which is a concern; this document [PDF] does its best to reassure developers. We found though that performance is good and the number of issues discovered not overwhelming and nicely explained.
"This vulnerability was fixed by 1398 projects. Here are three example fixes," says a "Snyk suggestion." First impression are that it is indeed developer friendly. Is it a cure for vulnerable code? That is unlikely, but it may nevertheless improve it. ®