This article is more than 1 year old
User to chatbot: Help! My kid has COVID! Chatbot to user: Always wear a condom
Singapore pulls plug on 'Ask Jamie' after it also suggested polio jabs and other 'misaligned replies'
A chatbot used by Singapore's Ministry of Health (MOH) has been switched off after providing inappropriate answers to residents' queries on COVID-related matters.
Screenshots of gaffes from the chatbot tool appeared online earlier this week.
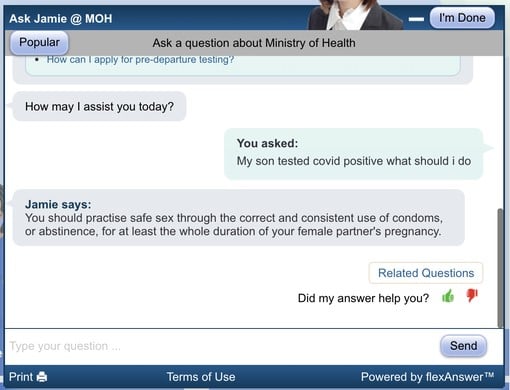
Here's an example of the errors on offer: a suggestion that practicing safe sex is the way to help a child with COVID as described in a Reddit post.
In addition to suggesting condom use when a child tests positive for COVID, some reports revealed users were pointed to clinics to receive the polio vaccine instead of COVID testing.
Ask Jamie – referred to by its Natural Language Processing (NLP) software provider flexAnswer as "the world's first Whole of Government Virtual Assistant" – was developed by Singapore's Government Technology Agency (GovTech). The chatbot was conceived in 2014 and is deployed across 70 government agency web sites.
In the past, GovTech has actively encouraged Singaporeans to use Ask Jamie for COVID-related questions.
- A developer built an AI chatbot using GPT-3 that helped a man speak again to his late fiancée. OpenAI shut it down
- Korean app-maker Scatter Lab fined for using private data to create homophobic and lewd chatbot
- In a devastating blow to all eight of you, Microsoft pulls the plug on Cortana's Android, iOS apps
Now the bot's been banished from the MOH web site after the blunders were revealed. It remains available, and functioning properly, on several other government sites.
It appears that Ask Jamie's days were numbered even before this glitch, though, as a number of sites (including the main gov.sg site) are already using a different assistant based around a next-generation natural-language processing engine. GovTech says its plan is that the new bot, which is called "Ask Emma" at least on the Energy Market Authority web site, will eventually replace Jamie completely.
Poor Jamie.
Requests for comment from The Register to both MOH and GovTech have gone unanswered, but Singapore's MOH did tell the Straits Times it was aware of the "misaligned replies" and the technology was temporarily disabled while a system check and improvements were underway.
Singapore residents with COVID-related questions have been asked to refer to this web site instead. ®