This article is more than 1 year old
Schools email marketing company told us to go away when we told them of exposed database creds, say infoseccers
Usernames and passwords could be read (and abused) by anyone in since fixed flaw
An email marketing company claiming to hold details on a million UK teachers and school admin personnel was potentially exposing those to the public internet thanks to a misconfigured error page on its website.
Not only that, but the Schools Marketing Company (SMC) seemingly dismissed the findings of the infosec company which spotted the flaw when the infoseccers tried to draw its attention to the problem.
An email shown to The Register by Pen Test Partners, described by the firm's consultant Andrew Tierney as "the most arrogant response I've ever had to a disclosure," said the company wasn't interested in hearing about the vulnerability.
What Tierney said he stumbled across was a server error message that displayed an awful lot of information to the public internet, including what appeared to be database usernames and passwords.
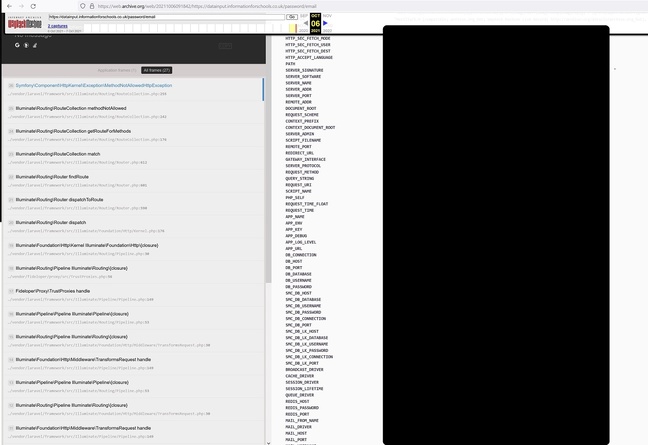
Schools Marketing Company's exposure of server login credentials, captured by archive.org. Click to enlarge
Upon reporting this to Leytonstone-based SMC, however, things didn't go as expected, said PTP. After repeated efforts to contact the company, a senior IT employee eventually replied to say:
Thank you for your email, and the subsequent one, and the one after that. You mention the word 'Chasing', what exactly are you 'chasing'?
You sent us an email, we were not interested in discussing the contents of the email and as far as we are concerned the matter is closed.
Please do not continue to contact us except to acknowledge this email.
El Reg has seen the full email, complete with names and signature blocks.
SMC's response surprised Tierney, who told The Register: "We've disclosed hundreds of issues over the years, but this ranks as one of the worst responses to date. The most obvious issue – the error page – is easier to fix than sending a snarky response. It's a bit worrying for a company that claims to hold contact details of over a million school staff."
It is unclear for how long the credentials were in the public domain but it was long enough for them to be indexed by the Internet Archive's Wayback Machine.
Thankfully, it appears the firm ultimately acted on the infoseccers' warnings.
Although The Register shared the Wayback Machine link with the SMC last week, the company did not initially reply – but as of yesterday morning the page at that URL displayed the message "Sorry. This URL has been excluded from the Wayback Machine."
- Things that are not PogChamp: Amazon's Twitch has its source code, streamer payout data leaked
- Telegraph newspaper bares 10TB of subscriber data and server logs to world+dog
- Emails, chat logs, more leaked online from far-right militia linked to US Capitol riot
- Story of the creds-leaking Exchange Autodiscover flaw – the one Microsoft wouldn't fix even after 5 years
Exposing the database username and password means anyone who could gain access to the firm's internet-facing login page could then read and copy its contents. The Schools Marketing Company website boasts that it is "GDPR and PECR compliant, registered with the Information Commissioner (ICO) since 2007" and that it has "over one million personal, school emails for UK teachers and staff, working in over 250 job function areas in schools."
Most companies receiving a disclosure from a reputable firm tend to take it seriously – with the best in the industry having proper vuln disclosure policies and a security.txt file. That being said SMC did act on the disclosure.
The ICO has been made aware of the potential breach and confirmed that Schools Marketing Company is a registered data processor. The regulator has the power to investigate and can issue fines if it believes wrongdoing or malpractice was involved in any proven data breach.
The Schools Marketing Company's system manager Tom Glasson today sent us a statement via email:
"We have no prior relationship with Pen Test Partners and we do not hold any confidential information on any of our servers, however, we took the matter seriously and have taken and are taking steps to ensure security of our systems as we always have done.
"There is no indication that any systems or information we hold have / has been compromised," he added. ®
