This article is more than 1 year old
Alibaba Cloud drops all-in-one client device, on-prem cloud-native DB
Claims shared memory speed breakthrough in new server, plans to enter South Korea and Thailand, and more
Announcements were coming thick and fast at Alibaba Cloud's annual APSARA conference, where the Middle Kingdom's biggest cloud unleashed an all-in-one client device, plenty of upgrades to its cloud services, and an uncanny weather predictor.
The Chinese cloud leader last year gave the world "Wuying" – a tiny device that provided on-prem access to a PC running in its cloud. Last year's Wuying offered a USB-C port to connect it to the required external display (as demonstrated in this video).
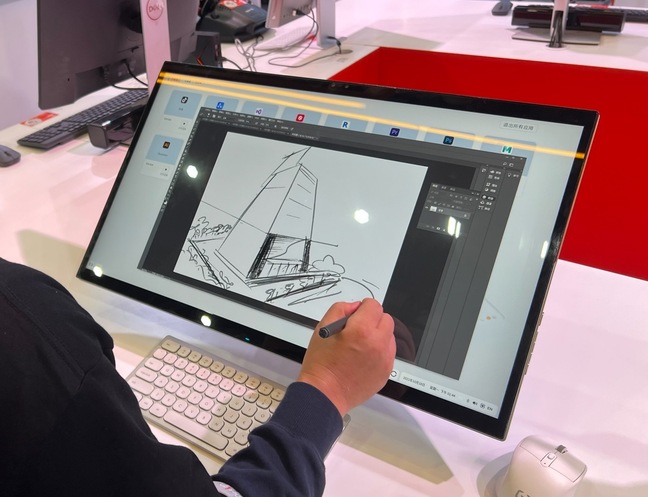
2021's model is an all-in-one device. Here it is in all its glory.
To make Wuying more attractive in all form factors, Alibaba Cloud has also created what it calls a "Cloud Workplace" that offers cloud storage and allows creation of security policies for remote workers. The company suggests the service as ideal for organisations that are managing remote workforces, and also want the access control and DR capabilities they'd build for an on-prem environment.
Alibaba has also announced it is expanding its cloud into South Korea and Thailand – a further sign of its ambitions to become a dominant player in Asia.
The datacentres slated for those nations will have some interesting kit inside, including a new version of the firm's Shenlong design for in-house servers. Claimed performance is three million IOPS for storage and 50 million packets per second, with latency for those workloads capable of falling to 30 and 16 microseconds respectively.
How did Alibaba Cloud get so fast? The business unit claimed it's developed "the industry's only large-scale Remote Direct Memory Access (RDMA) networking capability with a latency as low as 5 microseconds". RDMA lets one machine use memory from another and can help to scale memory so that applications that need it aren't tied to particular hardware.
- Alibaba Cloud unveils home-spun 128-core Arm-compatible server processor
- Alibaba Cloud quietly tests desktops-as-a-service
- Alibaba Cloud growth slows after mystery international customer - maybe ByteDance - quits over ‘non-product related’ factors
Also new is "DBStack" – a Kubernetes-based cloud-native database that runs on-prem. Alibaba Cloud’s aim here is to offer cloud-native tech for the cloud-curious, before they're comfortable ascending. Ali’s PolarDB has also been upgraded, apparently by "further decoupling of memory and CPU cores" so that each can be scaled independently.
Also revealed at the conference was a weather forecasting service in the Cloud (what better place for it) claimed to be capable of predicting conditions six hours into the future. The service can also produce high-res imagery of weather conditions every ten minutes, at a resolution of 1km x 1km. It's available only in China, where Alibaba expects the nation's farmers will use the service to level-up their operations.
Details of the above are all scanty. Much of the Apsara conference is simultaneously translated, but deep dives on the new tech were not offered to The Register and documentation is limited in any language. As Alibaba has big ambitions for its gathering Cloud, we'll try to learn more – and to take a Wuying device for a spin. ®